
Subscribe to my newsletter, The Wavelength, if you want the content on my blog delivered to your inbox four times a week before it’s posted here. The Wavelength will transition to a subscription product early in 2022. Details to come.
Other Developments
- Apple will delay the proposed changes to its products designed to find Child Sexual Abuse Material (CSAM). In an amendment to its original press release, Apple stated:
- Previously we announced plans for features intended to help protect children from predators who use communication tools to recruit and exploit them and to help limit the spread of Child Sexual Abuse Material. Based on feedback from customers, advocacy groups, researchers, and others, we have decided to take additional time over the coming months to collect input and make improvements before releasing these critically important child safety features.
- The Office of Management and Budget (OMB) and Office of Science and Technology Policy (OSTP) issued a memorandum detailing the Biden Administration’s “Multi-Agency Research and Development Priorities for the FY 2023 Budget.” The agencies explained:
- This memorandum outlines the Administration’s multi-agency R&D priorities for formulating fiscal year (FY) 2023 Budget submissions to the Office of Management and Budget (OMB). The priorities covered in this memo require continued investments in R&D; science, technology, engineering, and mathematics (STEM) education and engagement; STEM workforce development; technology transfer and commercialization; and research infrastructure, with emphasis on Historically Black Colleges and Universities, other Minority Serving Institutions, and disadvantaged communities who have been historically underserved, marginalized, and adversely affected by persistent poverty and inequality. These priorities should be addressed within the FY 2023 Budget guidance levels provided by OMB.
- The agencies highlighted the White House’s priorities:
- Catalyze research and innovation in critical and emerging technologies. Agencies should collaborate to promote world-leading research and innovation boosting American industries and quality American jobs in critical and emerging technologies, including artificial intelligence (AI), quantum information science (QIS), advanced communications technologies, microelectronics, high-performance computing, biotechnology, robotics, and space technologies. Agencies should coordinate to leverage these technologies to ensure the sharing and use of the vast troves of Federal Government datasets to enable large-scale data analysis, and high-fidelity, high-resolution modeling and simulation to address critical challenges in public health, climate science, and disaster resilience. Agencies should actively pursue public-private partnerships, as allowable, that will expedite American leadership in these technologies to grow our inclusive 21st- century digital economy. Within the area of AI, agencies should prioritize fundamental and translational AI research consistent with the Administration’s priorities for robust, safe, secure, and privacy preserving machine learning. Within the area of QIS, agencies should prioritize programs to deliberately address the hardest scientific and engineering problems facing the field.
- National security and economic resilience. Agencies’ plans and budgets should support the research, development, and application of technologies that protect American security and strengthen our economic resilience. Investments in security should prioritize the reduction of catastrophic biological, nuclear, and cyber risks, including investments in technologies supporting: biosecurity and biosafety; nuclear nonproliferation, arms control and treaty verification, measures that lower the risk of nuclear accidents and miscalculation, and measures that enhance strategic stability; and new capabilities for defending critical infrastructure and sensitive networks against cyberattacks and supply chain attacks, including improved authentication mechanisms, zero-trust architectures, and better intrusion detection capabilities. Investments in economic resilience should emphasize technologies that ensure safe, clean, and reliable access to critical products, materials and minerals, including new manufacturing and biomanufacturing processes that can cost-effectively produce key goods on demand.
- The British government announced its “post-Brexit global data plans to boost growth, increase trade and improve healthcare.” The United Kingdom’s (UK) Department for Digital, Culture, Media & Sport (DCMS) issued guidance titled “International data transfers: building trust, delivering growth and firing up innovation” and a map of UK data partnerships. DCMS explained:
- The government is outlining the first territories with which it will prioritise striking ‘data adequacy’ partnerships now it has left the EU as the United States, Australia, the Republic of Korea, Singapore, the Dubai International Finance Centre and Colombia.
- It is also confirming that future partnerships with India, Brazil, Kenya and Indonesia are being prioritised.
- These new data adequacy partnerships, which will be subject to assessments that ensure high data protection standards, will build significantly on the £80 billion of data-enabled service exports to these 10 destinations from the UK every year.
- Estimates suggest there is as much as £11 billion worth of trade that goes unrealised around the world due to barriers associated with data transfers*.
- The aim is to move quickly and creatively to develop global partnerships which will make it easier for UK organisations to exchange data with important markets and fast-growing economies. These new partnerships will build on the existing 42 adequacy arrangements the UK has in place with countries around the world.
- It is part of new plans to use the power of data to drive growth and create jobs while keeping high data protection standards. It will work hand in hand with the UK’s trade agreements and support the country’s ambitious trade agenda to unlock data flows and minimize unjustified barriers or conditions.
- United States (U.S.) Senators Amy Klobuchar (D-MN) and John Thune (R-SD) wrote TikTok Chief Executive Officer Shou Zi Chew “requesting information about the company’s collection of consumer data, including facial and voice biometrics.” They claimed:
- TikTok recently changed its U.S privacy policy to enable its app to automatically store certain physical and behavioral characteristics taken from users’ content. In the letter, the senators asked the company to answer a series of questions about the collection and use of this data, actions it is taking to ensure user data is secure, and its policies and practices regarding sharing data with third parties.
- They stated in the letter:
- We write to express our serious concerns regarding reports of TikTok’s updated privacy policy which allows for the collection of user data, including facial and voice biometrics. We request more information to ensure consumers’ data privacy is protected.
- Protecting consumers’ privacy is a top priority. Given the seriousness of this issue, we request that you provide answers to the following questions by August 25, 2021:
- What constitutes a “faceprint” and “voiceprint”? Please provide definitions of these terms and describe how this data will be used. Will it be shared with third parties? How long is this data retained?
- Is TikTok collecting this data for users under the age of 18?
- Your privacy policy states that TikTok may collect image and audio information for “content and ad recommendations.” Please provide a description of TikTok’s process for recommending content and advertisements.
- Does TikTok make any inferences about its users based on faceprints and voiceprints? If so, please describe those in detail.
- Does TikTok use machine learning to determine a user’s age, gender, race, ethnicity, or other characteristics observed from faceprints and voiceprints? If so, what steps has TikTok taken to audit the machine learning process for accuracy and bias?
- Please provide a list of all the entities (including parent organizations) that have access to the data collected by TikTok.
- The United Kingdom’s Information Commissioner’s Office (ICO) provided its thinking on what comes next now that the Age appropriate design code (aka the Children’s Code) has come into effect in the UK:
- The transition year is up and the Children’s code comes fully into force on 2 September. It’s a ground breaking code that creates a better internet for children by ensuring online services likely to be accessed by children, respect a child’s rights and freedoms when using their personal data.
- As you’d expect it’s already having an impact on these services. Facebook, Google, Instagram, TikTok and others have all made significant changes to their child privacy and safety measures recently.
- As the first-of-its kind, it’s also having an influence globally. Members of the US Senate and Congress have called on major US tech and gaming companies to voluntarily adopt the standards in the ICO’s code for children in America. The Data Protection Commission in Ireland is preparing to introduce the Children’s Fundamentals to protect children online, which links closely to the code and follows similar core principles.
- Post 2 September the risks to children are not removed overnight, and the work doesn’t stop.
- We have identified that currently, some of the biggest risks come from social media platforms, video and music streaming sites and video gaming platforms. In these sectors, children’s personal data is being used and shared, to bombard them with content and personalised service features. This may include inappropriate adverts; unsolicited messages and friend requests; and privacy-eroding nudges urging children to stay online. We’re concerned with a number of harms that could be created as a consequence of this data use, which are physical, emotional and psychological, and financial.
- Children’s rights must be respected and we expect organisations to prove that children’s best interests are a primary concern. The code gives clarity on how organisations can use children’s data in line with the law, and we want to see organisations committed to protecting children through the development of designs and services in accordance with the code.
- We will be proactive in requiring social media platforms, video and music streaming sites and the gaming industry to tell us how their services are designed in line with the code. We will identify areas where we may need to provide support, or should the circumstances require, we have powers to investigate or audit organisations.
- Separately, we are considering how organisations in scope of the Children’s code can tackle age assurance, whether that’s verifying ages or age estimation. The ICO will be formally setting out its position on age assurance in the autumn.
- Our commitment to working with other regulators through the Digital Regulation Cooperation Forum (DRCF) will help ensure consistency between the code and the incoming online safety laws that will jointly protect children online.
- Ultimately the Children’s code will help industry innovate to ensure that the best interests of the child are a primary concern online and built into the design from the beginning. This will grow the trust between online services, children, parents and society.
- Two United States (U.S.) agencies announced far more requests for funding than they can accommodate for two broadband programs:
- The U.S. Department of Commerce’s National Telecommunications and Information Administration (NTIA) announced “that it has received more than 230 applications for the Broadband Infrastructure Program, for a total of more than $2.5 billion in funding requests across 49 states and U.S. territories.”
- The Federal Communications Commission (FCC) announced “that it has received requests for $5.137 billion to fund 9.1 million connected devices and 5.4 million broadband connections as part of the $7.17 billion Emergency Connectivity Fund Program.” The FCC added:
- The first filing window, which closed August 13, 2021, attracted applications from all 50 states, American Samoa, Guam, Northern Mariana Islands, Puerto Rico, U.S. Virgin Islands and the District of Columbia – including schools and libraries in both rural and urban communities seeking funding for eligible equipment and services received or delivered between July 1, 2021 and June 30, 2022.
- In view of outstanding demand and the recent spike in coronavirus cases, the FCC will open a second application filing window for schools and libraries to request funding for connected devices and broadband connections for off-campus use by students, school staff, and library patrons for the current 2021-22 school year.
- New Zealand’s Privacy Commissioner announced that “[t]he Government has introduced mandatory record keeping at specified places and events.” The Privacy Commissioner stated:
- People responsible for these places or gatherings (referred to in this guidance as ‘organisations’) must make sure they have safe and secure systems and processes in place so that everyone working on or visiting the premises can scan in or provide their details in an electronic or paper-based manual process, no matter how long they are there for. This includes workers, contractors, customers, and volunteers. At Alert Levels 3 and 4 some businesses and workplaces have extra requirements to support contact tracing.
- Please visit the Unite Against COVID-19 website for more information about the new requirements and to see if your organisation is required to comply with the order.
- Organisations need to ensure that their systems and processes for record keeping comply with the Privacy Act 2020. This includes ensuring that the information is held securely and cannot be seen or accessed by people who do not need to see it, including other customers or visitors. The paper customer sign-in registers that have previously been used by some organisations are not compliant (as the contact record information is visible to other customers) and need to be replaced with other processes and systems.
- Unite Against COVID-19 resources are available here.
- The following advice is to help you comply with the requirements of the Privacy Act while complying with the new record keeping requirements.
- The Department of Homeland Security’s (DHS) Office of the Inspector General (OIG) published an “Evaluation of DHS’ Compliance with Federal Information Security Modernization Act Requirements for Intelligence Systems for Fiscal Year 2020.” The OIG said in an unclassified summary:
- Since our FY 2019 evaluation, the Office of Intelligence and Analysis has continued to provide effective oversight of the department-wide intelligence system and has implemented programs to monitor ongoing security practices.
- We determined that DHS’ information security program for Top Secret/Sensitive Compartmented Information intelligence systems is effective this year as the Department achieved “Level 4 – Managed and Measurable” in three of five cybersecurity functions, based on current reporting instructions for intelligence systems. However, we identified deficiencies in DHS’ protect and recover functions.
- We made three recommendations to the Office of Intelligence and Analysis to address the deficiencies identified. The Office of Intelligence and Analysis concurred with all three recommendations.
- Australia’s the Office of the Australian Information Commissioner (OAIC) issued its latest Notifiable Data Breaches Report that “highlights how the OAIC expects entities to prevent and respond to data breaches caused by ransomware and impersonation fraud.” The agency explained:
- The OAIC received 446 data breach notifications from January to June 2021, with 43% of these breaches resulting from cyber security incidents.
- Data breaches arising from ransomware incidents increased by 24%, from 37 notifications last reporting period to 46.
- Australian Information Commissioner and Privacy Commissioner Angelene Falk said the increase in ransomware incidents was cause for concern, particularly due to the difficulties in assessing breaches involving ransomware.
- The OAIC was notified of a number of data breaches resulting from impersonation fraud, which involves a malicious actor impersonating another individual to gain access to an account, system, network or physical location.
- Other key findings:
- Malicious or criminal attacks remain the leading source of data breaches, accounting for 65% of notifications.
- Data breaches resulting from human error accounted for 30% of notifications, down from 203 to 134.
- The health sector remains the highest reporting industry sector (19% of all notifications), followed by finance (13%).
- The number of notifications varied across the reporting period, ranging from 45 in January – the lowest monthly total since the Notifiable Data Breaches scheme commenced – to 102 in March.
- 91% of data breaches involved contact information, making it the most common type of personal information involved in data breaches.
- 93% of data breaches affected 5,000 individuals or fewer, with 65% of breaches affecting 100 individuals or fewer. 44% of breaches affected between 1 and 10 individuals.
- 72% of entities notified the OAIC within 30 days of becoming aware of an incident that was subsequently assessed to be an eligible data breach.
- While human error breaches decreased after a significant increase last reporting period, Commissioner Falk said entities need to remain alert to this risk, particularly the Australian Government where 74% of breaches fell into this category.
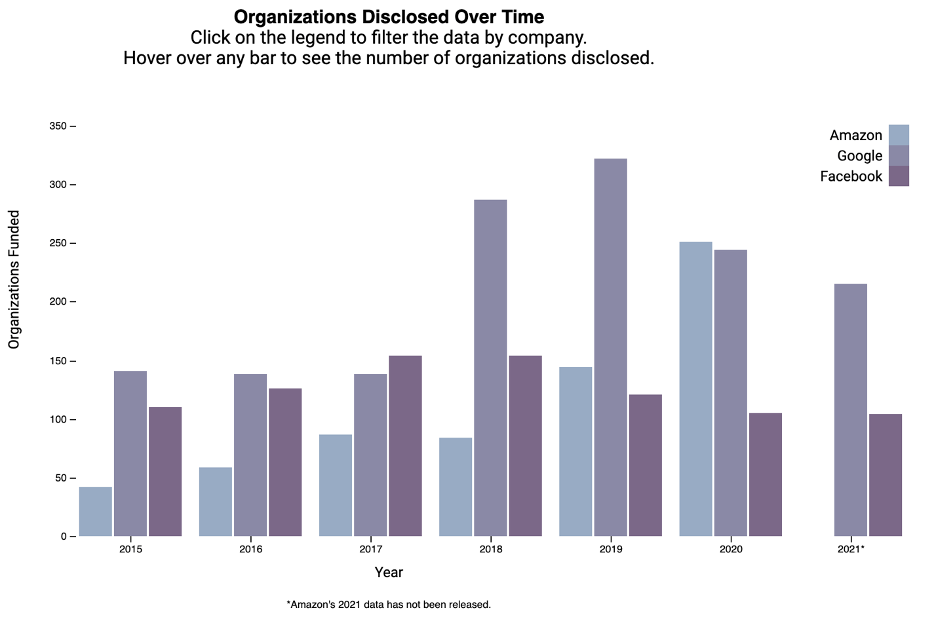
- The Tech Transparency Project (TTP) released a “searchable database” that “gives a quick readout on whether [think tanks, advocacy organizations and others] have received funding from the tech companies since 2015.” TTP asserted:
- With data from Facebook, Google, and Amazon going back to 2015, this tool provides the most comprehensive historical look at tech company giving to nonprofits to date.
- Some caveats: The database includes U.S. organizations that the three tech companies have voluntarily disclosed funding between 2015 and 2021, and it may not capture the full extent of Big Tech-funded groups. In the future, however, TTP plans to expand this database with additional details culled from media reports and nonprofit IRS 990 forms as well as other sources. TTP also plans to add information about Apple-funded groups.
- The database includes 2021 disclosures by Google and Facebook, but not by Amazon, which has yet to release its list of third-party funding recipients this year. TTP will update the database with new company disclosures as they become available.
- TTP released this chart:
- California Attorney General Rob Bonta “issued guidance today to healthcare facilities and providers reminding them of their obligation to comply with state and federal health data privacy laws.” In his press release, Bonta stated:
- In a bulletin sent to stakeholder organizations, including the California Hospital Association, the California Medical Association, and the California Dental Association, the Attorney General reminded healthcare entities that they must notify the California Department of Justice (DOJ) when the health data of more than 500 California residents has been breached. Today’s bulletin comes on the heels of multiple unreported ransomware attacks against California healthcare facilities
- The healthcare sector has been a main target of multiple cyberattacks. Last year, the U.S. Cybersecurity and Infrastructure Security Agency, the Federal Bureau of Investigation, and the U.S. Department of Health and Human Services released a joint report that stated the agencies had “credible information of an increased and imminent cybercrime threat to U.S. hospitals and healthcare providers.” These cyber attackers often introduce malware, including ransomware into a computer system to render health data files and systems useless and hold the data hostage in exchange for a ransom. When the breaches of data involve Social Security numbers, health records, or other sensitive information, they threaten the privacy, security, and economic wellbeing of impacted Californians. They also disrupt the ability of providers to provide care and erode patient trust.
- California law (Civil Code section 1798.82) requires entities that have suffered a data breach, including a health data breach, affecting more than 500 California residents to submit a breach report to the Office of the Attorney General. When healthcare providers notify the Attorney General of these breaches, the DOJ advises the public of the breach through the Attorney General’s website.
- In today’s bulletin, Attorney General Bonta also urged healthcare entities to take the following proactive steps, at minimum, to protect patient data from potential ransomware attacks:
- Keep all operating systems and software housing health data current with the latest security patches;
- Install and maintain virus protection software;
- Provide regular data security training for staff members that includes education on not clicking on suspicious web links and guarding against phishing emails;
- Restrict users from downloading, installing, and running unapproved software; and
- Maintain and regularly test a data backup and recovery plan for all critical information to limit the impact of data or system loss in the event of a data security incident.
- The United States Department of the Treasury’s Office of Foreign Assets Control (OFAC) and Department of Commerce’s Bureau of Industry and Security (BIS) published a fact sheet “to emphasize the U.S. government’s commitment to promoting the ability of the Cuban people to seek, receive, and impart information, by highlighting the most relevant exemptions and authorizations pertinent to supporting the Cuban people through the provision of certain internet and related telecommunications services.”
- Senate Commerce, Science, and Transportation Committee Ranking Member Roger Wicker (R-MS) wrote the Department of Commerce’s Bureau of Industry and Security (BIS) “inquiring about the implementation of a Final Rule restricting access by Huawei to U.S. technologies.” Wicker stated:
- The BIS plays a critical role in combatting threats to national security posed by Chinese companies and protecting the U.S. technology industry. To that end, the Department of Commerce issued a Final Rule further restricting access by Huawei to U.S. technologies by adding additional non-U.S. affiliates of Huawei to the Entity List, removing the Temporary General License for Huawei and replacing it with a more limited authorization, and expanding the scope of Foreign Direct Product Rule to tighten Huawei’s ability to procure items that are the direct product of specified U.S. technology or software.
- My staff contacted the BIS seeking details about the licensing component of the rule as part of ongoing oversight about compliance with this rule by leading hard disk drive suppliers. Following an informal briefing, officials claimed that the information sought by staff is subject to Section 1761(h) of the Export Control Reform Act of 2018, which allows the Bureau to withhold certain information based on confidentiality concerns. However, the information requested neither focused on any particular company’s compliance nor could have resulted in a breach of confidentiality for a company under investigation.
- My staff has reviewed evidence suggesting possible non-compliance with this rule. As part of my investigation, I request responses to the following questions so my staff can ensure Huawei is not gaining unlawful access to U.S. technologies:
- How many companies have sought a license to ship to Huawei or its affiliates under this Final Rule?
- How many of those applications have been processed and granted?
- How many applications have been denied?
- The National Security Agency updated its FAQs on “Quantum Computing and Post-Quantum Cryptography.”
Further Reading
- “The Texas abortion ban could force tech to snitch on users” By Issie Lapowsky — Protocol. With the Supreme Court deciding not to block Texas’ effective ban on abortion this week, fears have been rightly focused on the people in Texas who will be almost entirely barred from receiving an abortion in the state and the providers who will face grave legal consequences for continuing to provide services there. But the law’s construction creates a far broader surface area of risk than even that, enabling anyone to be sued for — knowingly or unknowingly — aiding and abetting the “performance or inducement” of an abortion. As some have pointed out, that tie could be as indirect as an Uber driver giving a woman a ride to a clinic.
- “Influencers Say A Sex Toy Company Has Been Hiring Them To Market Its Products But Delaying Paying Them” By Tanya Chen — BuzzFeed News. Influencers say a high-end sex toy company based in Melbourne has been hiring them to create sponsored content for its products — but then delaying or ghosting them when it’s time to pay up. Ooh! Companion touts itself as a company dedicated to “sexual empowerment” for women and sells vibrators that retail for hundreds of dollars on its website. But creators who have worked with the company on sponsored content deals told BuzzFeed News they have spent weeks or months chasing down payments from the brand, with some saying they were only paid after threatening legal action. Some have still never been paid in full.
- “Digital State IDs Start Rollouts Despite Privacy Concerns” By Elizabeth Montalbano — Threat Post. Eight states are introducing drivers licenses and identification cards available for use on Apple iPhones and Watches, but critics warn about the dangers of eliminating the use of a paper-based system entirely. Apple has unveiled the first eight states that will roll out digital IDs and drivers licenses on its mobile devices, despite critics’ concerns that the introduction of purely digital forms of identification will raise privacy, security and equanimity issues.
- “How to Repurpose Your Old Gadgets” By David Nield — WIRED. Electronic waste is a huge problem, one that’s getting worse: We’re now producing 21 percent more e-waste globally than we were five years ago. When it comes to gadgets like phones, your brand new model will likely be superseded in a year, and sometimes not even that. That’s why it’s worth thinking twice about what you do with your old gadgets whenever something new arrives. You might be surprised at how many ways you can repurpose an old piece of hardware, even if it’s several years old and has become too slow to fulfill its original function properly anymore.
- “Microsoft warns thousands of cloud customers of exposed databases” By Joseph Menn — Reuters. Microsoft on Thursday warned thousands of its cloud computing customers, including some of the world’s largest companies, that intruders could have the ability to read, change or even delete their main databases, according to a copy of the email and a cyber security researcher. The vulnerability is in Microsoft Azure’s flagship Cosmos DB database. A research team at security company Wiz discovered it was able to access keys that control access to databases held by thousands of companies. Wiz Chief Technology Officer Ami Luttwak is a former chief technology officer at Microsoft’s Cloud Security Group.
- “This is the real story of the Afghan biometric databases abandoned to the Taliban” By Eileen Guo and Hikmat Noori — MIT Technology Review. As the Taliban swept through Afghanistan in mid-August, declaring the end of two decades of war, reports quickly circulated that they had also captured US military biometric devices used to collect data such as iris scans, fingerprints, and facial images.Some feared that the machines, known as HIIDE, could be used to help identify Afghans who had supported coalition forces. According to experts speaking to MIT Technology Review, however, these devices actually provide only limited access to biometric data, which is held remotely on secure servers. But our reporting shows that there is a greater threat from Afghan government databases containing sensitive personal information that could be used to identify millions of people around the country.
- “Google, Apple Hit by First Law Threatening Dominance Over App-Store Payments” By Jiyoung Sohn — The Wall Street Journal. Google and Apple Inc. will have to open their app stores to alternative payment systems in South Korea, threatening their lucrative commissions on digital sales. A bill passed Tuesday by South Korea’s National Assembly is the first in the world to dent the tech giants’ dominance over how apps on their platforms sell their digital goods. It will become law once signed by President Moon Jae-in, whose party strongly endorsed the legislation.
- “Facebook will finally add the WhatsApp privacy policy option we all want” By Chris Smith — BGR. Facebook’s big WhatsApp privacy policy controversy from the first half of 2021 was one of the biggest of the year. Facebook told WhatsApp users in early 2021 that they would have to agree to new terms of service. The new policy would allow Facebook to acquire WhatsApp user data. It would be for e-commerce features that not all WhatsApp users might use. But all of them would be forced to agree to the changes. Except for those in the EU where Facebook wouldn’t implement them. We then saw Facebook change its mind a few times on how it would enforce the privacy policy. It ultimately chose not to block WhatsApp access for those who did not accept the new terms. And, in the future, Facebook will finally make the privacy policy optional.
- “Hackers exploit WhatsApp modification tool to snoop on texts, force paid subscriptions” By Tim Starks — cyberscoop. A malicious version of a popular modification or “mod” of the encrypted messaging app WhatsApp is carrying a mobile trojan that can launch advertisements, issue paid subscriptions and intercept text messages, security researchers said Tuesday. According to Kaspersky, hackers inserted the Triada trojan into a modified version of FMWhatsapp, a WhatsApp mod. Such mods have a following among users who want to customize WhatsApp, such as being able to send larger files or apply custom animated themes.
- “Amid a surge in ransomware attacks, cities are taking some of the biggest hits” By Joseph Marks — The Washington Post. Ransomware attacks have become a scourge for local governments, robbing millions of dollars in ransom payments to hackers and recovery costs from the government entities that can least afford to pay them. Public reports show more than 400 such attacks have hit city and county governments in the United States since 2016, impeding emergency responders, stalling tax payments and forcing government offices back to pen-and-paper operations for weeks on end. That’s probably only a fraction of the true number of such attacks, in which hackers lock up computers and demand payments to unlock them, because many attacks are thought to go unreported.
- “DOD awards $1B contract to Peraton to counter misinformation” By John Hewitt Jones — cyberscoop. The Department of Defense has awarded a task order worth up to $979 million over a five-year period to Peraton to counter misinformation from U.S. adversaries. The contractor will provide services to U.S. Central Command and its mission partners with operational planning, implementation and assessment services.
Coming Events
- 9 September
- The House Science, Space, and Technology Committee will mark up its portion of the FY 2022 budget reconciliation package.
- The United Kingdom’s Digital, Culture, Media and Sport Committee will hold a meeting on the nomination of New Zealand’s Privacy Commissioner John Edwards to be the next UK Information Commissioner.
- 10 September
- The House Agriculture Committee will mark up its portion of the FY 2022 budget reconciliation package.
- 14 September
- The European Data Protection Board (EDPB) will hold a plenary meeting.
- 15 September
- The Federal Trade Commission (FTC) will hold an open meeting with the following tentative agenda:
- Proposed Policy Statement on Privacy Breaches by Health Apps and Connected Devices: The Commission will vote on whether to issue a policy statement on the importance of protecting the public from privacy breaches by health apps and other connected devices.
- Non-HSR Reported Acquisitions by Select Technology Platforms, 2010-2019: An FTC Study: Staff will present some findings from the Commission’s inquiry into large technology platforms’ unreported acquisitions, including an analysis of the structure of deals that customarily fly under enforcers’ radar. The public release of the report is subject to commission vote.
- Proposed Revisions to FTC Procedural Rules Concerning Petitions for Rulemaking: The Commission will vote on putting in place a process to receive public input on rulemaking petitions by external stakeholders.
- Proposed Withdrawal of 2020 Vertical Merger Guidelines: The Commission will vote on whether to rescind the Vertical Merger Guidelines adopted in June 2020 and the Commentary on Vertical Merger Enforcement issued in December 2020.
- The Federal Trade Commission (FTC) will hold an open meeting with the following tentative agenda:
- 28 September
- The Information Security and Privacy Advisory Board (ISPAB) will hold an open meeting and “The agenda is expected to include the following items:
- —Board Discussion on Executive Order 14028, Improving the Nation’s Cybersecurity (May 12, 2021) deliverables and impacts to date,
- —Presentation by NIST, the Department of Homeland Security, and the General Services Administration on upcoming work specified in Executive Order 14028,
- —Presentation by the Office of Management and Budget on Executive Order 14028 directions and memoranda to U.S. Federal Agencies,
- —Board Discussion on recommendations and issues related to Executive Order 14028.
- The Information Security and Privacy Advisory Board (ISPAB) will hold an open meeting and “The agenda is expected to include the following items:
- 30 September
- The Federal Communications Commission (FCC) will hold an open meeting. No agenda has been announced as of yet.
© Michael Kans, Michael Kans Blog and michaelkans.blog, 2019-2021. Unauthorized use and/or duplication of this material without express and written permission from this site’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to Michael Kans, Michael Kans Blog, and michaelkans.blog with appropriate and specific direction to the original content.
Photo by Kaleidico on Unsplash
Photo by Daniel Olah on Unsplash