
Subscribe to my newsletter, The Wavelength, if you want the content on my blog delivered to your inbox four times a week before it’s posted here. The Wavelength will transition to a subscription product early in 2022. Details to come.
The Federal Trade Commission (FTC) just reached its second settlement with a spyware company, with this one being more restrictive and far-reaching than the first in late 2019 under the former FTC chair. This settlement suggests a more aggressive agency willing to push for more punitive terms in order to punish the instant wrongdoers but also to signal to others that the FTC will use its full powers. Of course, the longstanding charge against the agency has been it smashes small offenders and treads lightly around bigger players, and this settlement will do little to dispel this perception. Nonetheless, the settlement suggests that new Chair Lina Khan and Commissioners Rebecca Kelly Slaughter and Rohit Chopra are willing to use authority the agency has not in recent years. It bears note that while the FTC voted 5-0 to approve this settlement, one should not conclude that Commissioners Noah Joshua Phillips and Christine Wilson are aligned with the Democratic majority. Rather their votes speak to the egregious and indefensible conduct the case presented.
In October 2019, in the FTC’s first spyware case, Retina-X Studios, LLC agreed to a consent order that permanently restrains and enjoins the company “from, or assisting others in, promoting, selling, or distributing a Monitoring Product or Service unless Respondents” meet a list of requirements, including foreswearing the circumvention of a mobile device’s operating system for installation (aka jail-breaking or rooting), eliciting affirmative agreement that users of any such app will only employ it in lawful, enumerated practices, and that whenever the app is running, there must be a clear and conspicuous icon on the device alerting the user that the run has been installed and is functional. The FTC required Retina-X Studios to
- Meet the requirements of the Children’s Online Privacy Protection Act (COPPA) rule
- Stop misrepresenting how they actually safeguard personal information
- Delete all the personal information collected from the three apps
- Implement a comprehensive data security program
- Pay for an initial and then biennial data assessments from a third-party assessor
- Submit annual certifications by a senior corporate official that the company is meeting the requirements of the settlement, and if not, there must be explanation of any such violations
- Alert the FTC within 10 days after personal data has been accessed or acquired without authorization
In the instant complaint, the FTC claimed the Support Kings/SpyFone offered Android spyware and advertised their app as being for surveilling employees and children. However, in truth, at least in the FTC’s telling of events, the main market for their spyware was for jealous and abusive spouses and partners to spy on and stalk their partners. This spyware could only be installed if a person could access someone else’s device and then required a number of surreptitious steps, some of which compromised the security of the device. Support Kings/SpyFone offered a number of different packages, and the most popular one included all of these options:


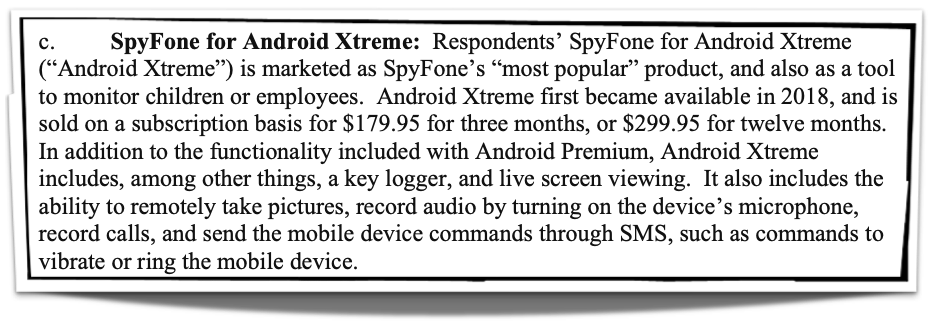
And so, users of this spyware could see and track virtually everything another person did on their phone, everywhere the person went, and all of their communications. Most troubling is the remote access to live screen or recording audio and calls.
The FTC took aim at Support King/SpyFone’s claims that its product was for employers and parents:
The purported use of the monitoring products and services for employment or child- monitoring purposes is a pretext. Parents and employers would not typically want the monitoring product to spoof text messages from the device, a feature SpyFone marketed to its customers, or want to disable security measures on a mobile phone to install Respondents’ Android monitoring products and services—particularly when doing so may void a warranty and weaken the mobile device’s security. Many other monitoring products are available in the marketplace that do not carry these risks.
The FTC’s investigation also turned up shoddy data security practices and misrepresentation of these practices, including after a breach, that are brazen. The company claimed it encrypted user data, but it did not. Also, after a breach involving over 2000 customers was discovered, the company falsely claimed to users that it had “partner[ed] with leading data security firms to assist in our investigation” and that they would “coordinate with law enforcement authorities” on the matter.”
Ultimately, the FTC alleged three violations of the FTC Act:

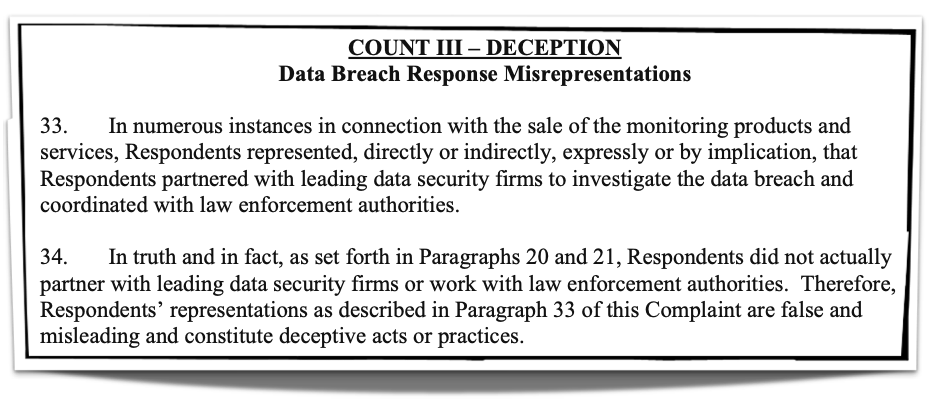
The FTC is arguing here that Support King/SpyFone violated both the unfair and deceptive practices prohibition in Section 5 of the FTC Act.
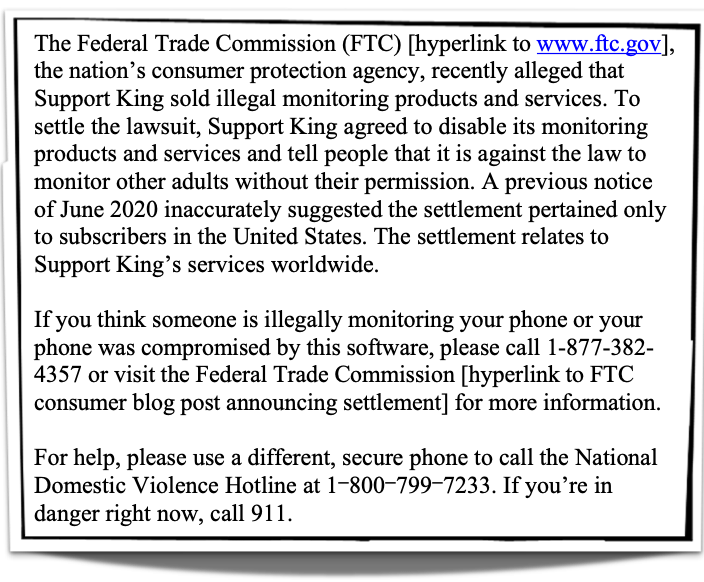
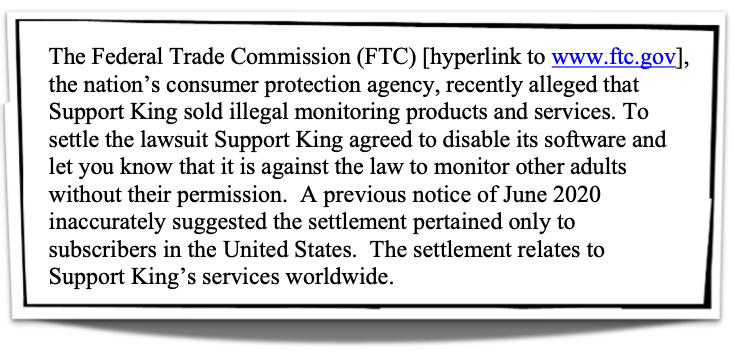
In the agreement and consent order, the FTC and Support King/SpyFone agreed to a slew of changes, including the company and its CEO, Scott Zuckerman, being “permanently restrained and enjoined from licensing, advertising, marketing, promoting, distributing, or offering for sale, or assisting in the licensing, advertising, marketing, promoting, distributing, or offering for sale, any Monitoring Products or Services to consumers.” The agency sought and obtained agreement from the company and its CEO to forever forgo the spyware market under pain of the FTC seeking civil penalties in federal court. The FTC also required Support King/SpyFone to post the following notices conspicuously on their website:
The company would need to email the following to anyone who bought the service:
In what may be a first with spyware in the United States (U.S.), the FTC is requiring Support King/SpyFone to push out an “on-screen notification to Mobile Device users with a Monitoring Product or Service installed on their Mobile Device prior to the entry of this Order, which shall Clearly and Conspicuously state:”

It is possible this notice would lead some of the victims to seek legal recourse including contacting the police and filing suit in civil court. This remains to be seen.
Moreover, Support Kings/SpyFone must immediately disable all access to information collected through the app, destroy all the personal information the company has on hand within 30 days, cannot misrepresent their activities or interactions with privacy and security firms or its own privacy and security activities, cannot “transfer, sell, share, collect, maintain, or store Personal Information unless it establishes and implements, and thereafter maintains, a comprehensive information security program,” obtain biennial security assessments by a third party and cooperate with this assessment process, and certify annually to the FTC the company is complying with the order. Moreover, in the event of any covered incidents[1], Support Kings/SpyFone must alert the FTC within 21 days in addition to the federal and state entities the company must also inform. The company will need to submit compliance reports to the FTC annually for ten years. Finally, the order is effective for 20 years.
As noted, this settlement suggests a more aggressive FTC. This settlement is like the one with photo app developer Everalbum that required “the company to delete models and algorithms it developed by using the photos and videos uploaded by its users” and mandated that the company must “obtain consumers’ express consent before using facial recognition technology on their photos and videos.” In that case, the agency wanted to ensure the company did not profit from its ill-gotten data. And the same is true here with Support Kings/SpyFone being forced to delete all user data, having to warn victims, and being permanently barred from the industry. In past settlements, companies would often be slapped on the wrist but not forced to delete or destroy the data or algorithms they obtained through their illegal conduct. This FTC thinks this requirement should be part of every data related settlement.
[1] “…any instance in which any United States federal, state, or local law or regulation requires Respondents to notify any U.S. federal, state, or local government entity that information collected or received, directly or indirectly, by Respondents from or about an individual consumer was, or is reasonably believed to have been, accessed or acquired without authorization.”
© Michael Kans, Michael Kans Blog and michaelkans.blog, 2019-2021. Unauthorized use and/or duplication of this material without express and written permission from this site’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to Michael Kans, Michael Kans Blog, and michaelkans.blog with appropriate and specific direction to the original content.
Photo by Julia Matuzova on Unsplash
Photo by alevision.co on Unsplash