
Subscribe to my newsletter, The Wavelength, if you want the content on my blog delivered to your inbox four times a week before it’s posted here.
At the end of July, the House of Representatives passed a package consisting of seven FY 2022 appropriations bills, including some of the bills that fund key agencies and programs with respect to technology. Today, we will dive into some of these bills, and it bears note the recent SolarWinds and Microsoft Exchange hacks shook up the House Appropriations Committee which is providing massive increases for a number of programs to secure networks and systems at United States (U.S.) agencies.
The “Financial Services and General Government Appropriations Act, 2022” (H.R.4345) funds and shape policy for the Federal Trade Commission (FTC), Federal Communications Commission (FCC), the Office of Management and Budget, and the new Office of the National Cyber Director (NCD). In the committee report, the committee hit some of the highlights of the bill:
- Protecting Consumers.—The Committee is concerned about ongoing consumer protection issues, including hidden and emerging product safety incidents, market concentration, privacy and data security violations, and instances of financial fraud. Consequently, the Committee recommendation provides significant additional resources to agencies responsible for overseeing product safety, fair competition, unfair and deceptive trade practices, and financial markets. The recommendation provides $172,000,000—an increase of $37,000,000 over fiscal year 2021—for the Consumer Product Safety Commission to address chronic underfunding in recent years and to expand operational capabilities to match the safety challenges in an evolving marketplace. The Committee expects that these additional resources will also allow improved consumer education on hidden and emerging hazards, especially in relation to toys and other products that pose a disproportionate risk for children, including crumb rubber.
- The Committee recommends $389,800,000—a $38,800,000 increase over fiscal year 2021—for the Federal Trade Commission (FTC). This additional funding will increase the FTC’s capabilities both to monitor mergers and acquisitions that could reduce com- petition or lead to higher prices, and to take enforcement action against companies that fail to take reasonable steps to secure customer data or that engage in other problematic trade practices. The Committee recommendation also increases resources to protect investors, facilitate capital formation, and combat market manipulation. To that end, the recommendation includes $1,999,663,000—an increase of $73,501,000 over fiscal year 2021—for the Securities and Exchange Commission to increase enforcement related to securities and financial fraud, monitoring of major market participants, compliance examinations, and investor education activities.
As the committee mentioned, the FTC would see another 10% year-over-year funding increase, in large part, because:
The Committee is highly concerned by increasing instances of fraudulent or deceptive data collection practices and other violations of consumer protection laws, as well as by increasing concentration in technology and other markets. The Committee provides the FTC with additional resources to increase both its enforcement of antitrust statutes and its capacity to investigate unfair, deceptive, and fraudulent business practices.
The committee provided the following additional direction for the FTC pertaining to shipping consumer goods outside the continental U.S., cryptocurrency, the right to repair, children’s privacy and the Children’s Online Privacy Protection Act Rule, and pirated and counterfeited goods in online marketplaces:
- Non-Foreign Areas.—The Committee remains concerned that some companies and corporations engaged in interstate commerce are unwilling to ship products to Alaska, Hawaii, Puerto Rico, and the other U.S. territories, as is offered for the continental United States, or are only willing to ship to these areas at significantly higher rates. The Committee believes that these non-foreign areas must be afforded equal treatment to the other 48 states. The Committee requests the FTC to continue monitoring these inequalities in interstate commerce and to continue issuing relevant outreach and educational materials.
- Cryptocurrency.—Cryptocurrencies are digital assets that use cryptography to secure or verify transactions. They are not created by a government or central bank, but they can be exchanged for U.S. dollars or other government-backed currencies. As consumer interest in cryptocurrencies has grown, so have scams such as deceptive investment and business opportunities, bait-and-switch schemes, and deceptively marketed mining machines. The Committee encourages the FTC to work with the Securities and Exchange Commission, other financial regulators, consumer groups, law enforcement, research organizations, and other public and private stakeholders to identify and investigate fraud related to cryptocurrencies market and discuss methods to empower and protect consumers. The Committee recommends that the FTC increase its engagement with stakeholders on this issue and that the FTC promptly publish any public education or consumer protection best practices developed from its activities on its website.
- Consumer Right to Repair.—The Committee is aware of the FTC’s ongoing work examining how manufacturers, particularly mobile phone and car manufacturers, may limit repairs by consumers and repair shops, and how those limitations may increase costs, limit choice, and impact consumers’ rights under the Magnuson-Moss Warranty Act. The Committee appreciates the FTC’s timely and comprehensive report, ‘‘Nixing the Fix: An FTC Report to Congress on Repair Restrictions,’’ issued in May 2021. The report notes that ‘‘[t]o address unlawful repair restrictions, the FTC will pursue appropriate law enforcement and regulatory options, as well as consumer education, consistent with our statutory authority.’’ The Committee requests a briefing, within 120 days of enactment of this Act, on law enforcement, regulatory, and educational actions the agency has taken in relation to the Magnuson-Moss Warranty Act since the publication of that report, including an assessment of how repair restrictions might impact rural communities, communities of color, and indigenous communities.
- Children’s Privacy.—The Committee is aware of the significant increase in online activity by children during the COVID 19 pandemic and is concerned that this may lead to a greater opportunity for bad actors to unlawfully gather and use children’s personal information. The Committee urges the FTC to prioritize investigations into potential violations of the Children’s Online Privacy Protection Act Rule (COPPA Rule) and to incorporate findings from new and recent cases relating to children’s privacy into its ongoing COPPA Rule review process. Not later than 120 days after the enactment of this Act, the FTC is directed to provide to the Committee a report detailing the current amount of resources and personnel focused on enforcing the COPPA Rule; the number of investigations into violations of the COPPA Rule in the past 5 years; and the types of relief obtained, if any, for any completed investigations.
- Online Marketplaces.—The Committee encourages the FTC to increase enforcement efforts to stop the sale of counterfeit and pirated goods on online marketplaces.
The Federal Communications Commission (FCC) would get $14 million more in funds than the current year ($387.95 million vs. $374 million), and the committee is very focused on how the agency is helping (and could maybe help even more) in ensuring broadband is widely available:
- Broadband Maps.—The Committee remains highly interested in implementation of the Broadband DATA Act (P.L. 116–130). The FCC is directed to provide an updated spend plan and status report on Broadband Data Act spending no later than 60 days after enactment of this Act.
- Mapping Partnership with USPS.—The Committee notes that the FCC released a report in May 2021 on the feasibility of partnering with the United States Postal Service to facilitate the collection of mobile wireless broadband data, as required by the Broadband DATA Act. The report outlines several challenges but says that ‘‘the Commission is continuing to explore possible solutions to the issues.’’ The Committee encourages the FCC to continue its work to address these obstacles and create a feasible partnership that will help improve wireless mapping in rural and underserved communities across the country.
- Broadband Access.—The Committee believes that deployment of broadband in rural and economically disadvantaged areas is a driver of economic development, jobs, and new educational opportunities. The Committee supports FCC efforts to judiciously allocate Universal Service Fund (USF) funds for these areas.
- Rural Digital Opportunity Fund.—In the Rural Digital Opportunity Fund (RDOF) Phase I auction, 180 bidders won $9.2 billion over 10 years to provide broadband to more than 5 million locations in U.S. States and territories. The RDOF Phase I auction rep- resents an opportunity to bring broadband access to unserved rural communities across this country and to help close the digital divide in rural communities, but the Committee remains concerned about program implementation. The Committee expects the FCC to fully enforce its rules related to buildout requirements and performance tier commitments.
- Territorial Access to Broadband.—The Committee is concerned about disparities in access to communications services on Tribal lands and in territories. The Committee encourages the FCC to implement policies to increase broadband access and adoption in these areas. The Committee commends the FCC’s work in establishing the Uniendo, a Puerto Rico Fund, and the Connect U.S. Virgin Islands (USVI) Fund to make additional USF funding available to rebuild fixed and mobile voice and broadband networks damaged in the 2017 hurricane season. In September 2019, the FCC approved $950,000,000 in Stage 2 funding to improve, expand, and harden communications networks in Puerto Rico and the USVI. In the U.S. Virgin Islands, the FCC is allocating more than $180,000,000 over ten years in support fixed networks, and $4,000,000 over three years for mobile networks. The Committee supports these efforts and urges the FCC to expeditiously move forward with its funding commitments under these programs.
- Tribal Access to Broadband.—The Committee urges the FCC to responsibly and efficiently take action to increase access to broadband on Tribal lands and supports consultation with Federally recognized Indian Tribes, Alaska Native villages and corporations, and entities related to Hawaiian home lands to help close the digital divide. The FCC is encouraged to use all available resources to increase funding for consultation with Federally recognized Indian tribes, Alaska Native villages, and entities related to Hawaiian home lands; other work by the Office of Native Affairs and Policy (ONAP); and associated work from other bureaus and offices in support of ONAP.
- School Broadband.—The Committee believes that access to broadband is an important factor in student success in school. The coronavirus pandemic highlighted this issue, but it will continue for many students even after full-time remote learning ends. The Committee notes that Congress established a $7,171,000,000 Emergency Connectivity Fund in the American Rescue Plan Act of 2021 (P.L. 117–2) to help address this issue. The Committee directs the FCC to evaluate new or existing programs that could be used to permanently extend telecommunications and information services to students at locations other than schools and libraries. The Committee directs the FCC to provide a briefing on implementation of the Emergency Connectivity Fund and any findings from its evaluations no later than 120 days after the enactment of this Act.
The committee also directed the FCC on other policy areas, including telehealth, 5G, supply chain, cybersecurity, and municipal broadband:
- Telehealth Funding.—The Committee notes that the Consolidated Appropriations Act, 2021 (P.L. 116–260) required that ‘‘To the extent feasible, the Commission shall ensure, in providing assistance under the COVID–19 Telehealth Program . . . that not less than 1 applicant in each of the 50 States and the District of Columbia has received funding from the Program since the inception of the Program, unless there is no such applicant eligible for such assistance in a State or in the District of Columbia.’’ The Committee is pleased that the FCC has decided to adopt rules that ‘‘seek to ensure that at least two applications with lead health care providers from every state, territory, and the District of Columbia receive Program funding, if such applications exist.’’ The Committee supports the FCC’s decision to include all territories of the United States in its rule adoption.
- 5G Networks.—The Committee remains concerned about the digital divide and supports measures to bring broadband services to unserved and underserved communities as well as to address broadband affordability and adoption. The Committee also recognizes that ensuring the United States is the global leader in the 5G economy is an economic and national security imperative. The Committee supports policies to ensure that 5G technologies are developed domestically and among our allies, and that the United States leads the world in the deployment of multiple, facilities- based commercial 5G networks. To that end, the Committee supports a phased approach to making additional spectrum available for commercial licensed and unlicensed use. Additionally, the Committee supports the Commission’s efforts to make more mid-band spectrum available for auction and flexible commercial use. The Committee opposes efforts to use Federally allocated spectrum to create a national wholesale 5G network owned, operated, or controlled by the government and continues to support private sector efforts to deploy 5G.
- 5G Supply Chain.—The Committee notes the importance of a secure 5G technology supply chain. The Committee encourages the FCC to investigate options for increasing supply chain diversity, bolstering competition in the 5G equipment market, and strengthening 5G network security via hardware and software solutions that use virtualization technology, open standard-based interfaces, and interoperable equipment.
- USF Contribution Reform.—In recognition of the ongoing rapidly changing communications industry landscape, the Committee believes it is imperative that the FCC work with the Federal-State Joint Board on Universal Service on recommendations for USF modernization, including contribution reform to ensure the long-term sustainability and viability of the USF programs and resolve inequities in the current contributions structure.
- Lifeline Participation.—According to Universal Service Administrative Company estimates, less than 30 percent of eligible households participate in the Lifeline program. The Committee encourages the FCC to expeditiously address all recommendations made in GAO Report 21–235 to increase consumer awareness of and improve user experience with Lifeline. The Committee also encourages the FCC to work with community-based organizations to conduct outreach in areas with large amounts of unserved eligible households about the availability of the Lifeline program.
- Cybersecurity Certification and Labeling.—The Committee encourages the FCC’s Office of Engineering and Technology to begin assessing existing cybersecurity certifications pertinent to critical infrastructure and to develop further informational and technological resources, as needed, to inform consumer and critical infrastructure owner and operator purchasing decisions for secure information and communications technologies.
- Cloud Migration.—The Committee recognizes the importance of cloud migration for continued FCC operations and cybersecurity. Throughout much of the last decade, the FCC has released plans for IT modernization and cloud migration with the intention of decreasing their data center footprint in accordance with the Data Center Optimization Initiative (DCOI) mandated by Federal Information Technology Acquisition Reform Act (P.L. 113–291). The FCC is directed to provide a report to Committee no later than 120 days after enactment of this Act on its plans for re-architecting legacy systems, moving to commercial cloud solutions, and complying with DCOI.
- Municipal Broadband.—The Committee urges the FCC to study the role of municipal-owned networks in expanding broadband access to unserved and underserved communities.
For the White House’s OMB, the committee addressed the following:
- Infrastructure-as-a-Service in Federal Procurement.—The Committee is aware that the procurement of information and communication technology (ICT) by Federal agencies is increasingly utilizing an infrastructure-as-a-service (IaaS) model where agencies no longer purchase outright computer hardware, peripherals, printers, servers, and software. The Committee notes the significant cost of ownership as well as important cybersecurity benefits of this IaaS acquisition model and encourages its continued and expanded use, but also recognizes the importance of facilitating small business competition for these ICT procurements. The Committee directs OMB to examine the government’s use of ICT IaaS procurements and the ability of small businesses to successfully compete for these types of contracts. OMB should report to the Committee within 120 days of enactment of this Act with suggestions on improvements to the IaaS procurement process to allow better com- petition for small businesses.
- Office of Manufacturing and Industrial Innovation.—The Committee supports creation of an independent office within the Executive Office of the President dedicated to manufacturing and industrial innovation. Such an office would provide manufacturing and industrial perspectives and advice to the President, develop a strategic national manufacturing policy for the United States, and engage in a comprehensive survey and cross-administration management of efforts to ensure global leadership in manufacturing critical to the long-term economic health and national security of the United States. The Committee will work with OMB and other EOP offices to ensure that such an office is authorized and funded in a timely manner.
OMB gets tasked with reporting on the cyber posture of U.S. agencies, notably how well they are complying with a Trump Administration executive order:
Federal and Critical Infrastructure Cybersecurity.—In recent months, the nation’s information technology and critical infrastructure—which support global food supply chains, transportation systems, healthcare providers, and more—have been subject to a disturbing uptick in ransomware and cyberattacks. Executive Order 13800, issued on May 11, 2017, directs agency heads to implement several risk management and cybersecurity measures, including the National Institute of Standards and Technology Framework for Improving Critical Infrastructure Cybersecurity. The Committee is concerned that agencies have not implemented these foundational cybersecurity measures, including the following risk-based vulnerability management practices: 1) discovering all assets connected to the agency’s network, 2) continuously assessing and monitoring these assets for cybersecurity vulnerabilities, 3) managing users to prevent exploitation from attackers, and 4) prioritizing remediation of identified cybersecurity vulnerabilities posing the greatest risk. OMB is directed to report, within 90 days of enactment of this Act, on the status of compliance with Executive Order 13800 by each applicable agency. The report shall identify risk management and cybersecurity compliance gaps and outline steps each agency must take to implement risk-based vulnerability management practices. The report shall include a timeline and cost estimates to meet the requirements set forth in Executive Order 13800.
Note OMB must inform the committee about the timeline and costs of complying with the 2017 executive order. It is not a good commentary on U.S. government cybersecurity that the committee is worried that agencies have not complied with a four year old directive from the then President.
The new Office of the National Cyber Director (NCD) would get $18.75 million, $3.75 million more than the Administration asked for, and the committee is asking NCD Chris Inglis and his staff to outline how they will spend these funds and how they will operate alongside with and coordinate other federal cybersecurity stakeholders:
- Cyber Coordination.—The Committee notes the increasing regularity of highly damaging cyberattacks, including attacks against critical U.S. infrastructure, and supports the creation of new Federal cyber policy expertise and capabilities. The Committee also notes that cyber policy functions are currently distributed among numerous Federal agencies and offices and seeks clarity on ONCD’s jurisdiction. The Committee directs ONCD to consult with OMB, the National Security Council, the Cybersecurity and Infrastructure Security Agency, the United States Intelligence Community, the Department of Defense, and other Federal departments and agencies, as appropriate, to ensure coordination of, and avoid unnecessary duplication of, the activities of the ONCD with the activities of other parts of the Federal government. The Committee directs ONCD to provide a briefing within 90 days of enactment of this Act outlining its spending plan for funding provided by this Act and delineating the specific responsibilities of ONCD in relation to other Federal departments and agencies.
The General Services Administration (GSA) received a directive on supply chain security as it relates to “commercial off-the-shelf supply chain management tools:”
- Supply Chain Security Pilot.—There is growing consensus in the Federal government that increased measures need to be taken to better identify and effectively respond to threats to the Federal government’s information technology, networks, and supply chains. Commercial off-the-shelf supply chain tools have been developed to address supply chain issues such as understanding supply chains with precision, identifying cyber or other threats to them, and providing continuous critical information for when specific threats are identified. GSA should, as a matter of policy, consider using commercial off-the-shelf supply chain management tools to accomplish government supply chain monitoring missions. To support the critical monitoring of government supply chain programs, the Committee includes $4,000,000 above the fiscal year 2022 budget request to provide funding for demonstrations and contracts to test and evaluate the utility of commercial solutions for supply chain risk management for the Office of Information Technology Category within the GSA Federal Acquisition Service.
- GSA’s Federal Acquisition Service has previously demonstrated similar technologies through its Information Technology Category but has been unable to transition these services into meaningful improvements to the Administration’s acquisition framework. The Committee further directs the Administrator of GSA to submit a strategy to Congress with the President’s fiscal year 2023 budget submission to Congress on how commercial off-the-shelf supply chain risk management tools has been implemented and how the program could be expanded to improve the Administration’s overall acquisition framework.
A GSA managed program that operates as a revolving fund other agencies can borrow from to modernize their information technology would see a modest bump above its current level of funding. However, the Biden Administration wanted $500 million for the Technology Modernization Fund (TMF), which is $450 million more than the committee decided upon. The TMF was recently given $1 billion in this year’s COVID stimulus package, which undoubtedly affected the House’s decision. Nonetheless, the committee stated:
- The Committee recommends $50,000,000 for the TMF. The Committee encourages GSA and the TMF Board to prioritize and fund those projects that have the most significant impact on mission enhancement and that most effectively modernize citizen-facing services, including updating public facing websites, modernizing forms, and digitizing government processes.
- The Committee notes that the TMF received $1,000,000,000 in funding in the American Rescue Plan Act of 2021 (P.L. 117–2). Additionally, GSA has noted they expect to allocate $250,000,000 in fiscal year 2021 and fiscal year 2022 for the TMF. The Committee supports additional funding requests in future fiscal years for the TMF.
The Election Assistance Commission (EAC) would get another $500 million for Election Security Grants, one of the primary means the U.S. government has used to address cybersecurity vulnerabilities in state and local election systems. The committee naturally has conditions its expects the agency and funds recipients to meet:
- The bill requires States to use payments to replace direct-recording electronic (DRE) voting machines with voting systems that require the use of an individual, durable, voter-verified paper ballot, marked by the voter by hand or through the use of a non-tabulating ballot marking device or system, and made available for inspection and verification by the voter before the vote is cast and counted. Funds shall only be available to a State or local election jurisdiction for further election security improvements after a State has submitted a certification to the EAC that all DRE voting machines have been or are in the process of being replaced.
- Funds shall be available to States for the following activities to improve the security of elections for Federal office: implementing a post-election, risk-limiting audit system that provides a high level of confidence in the accuracy of the final vote tally; maintaining or upgrading election-related computer systems, including voter registration systems, to address cyber vulnerabilities identified through DHS scans or similar assessments of existing election systems; facilitating cyber and risk mitigation training for State and local election officials; implementing established cybersecurity best practices for election systems; and other priority activities and in- vestments identified by the EAC, in consultation with DHS, to improve election security. The EAC shall define in the Notice of Grant Award the eligible investments and activities for which grant funds may be used by the States. The EAC shall review all proposed investments to ensure funds are used for the purposes set forth in the Notice of Grant Award.
- The bill also requires that not less than 50 percent of the payment made to a State be allocated in cash or in-kind to local government entities responsible for the administration of elections for Federal office. Further, the bill requires States to submit semi-annual financial reports and annual progress reports to the EAC.
The Committee further directed the EAC on these issues:
- Election Cybersecurity Support.—The Committee is concerned with the threat of election meddling from state and non-state actors through cyberattacks on election and voter registration systems. The Committee encourages EAC to work with NIST and the Department of Homeland Security (DHS) to strengthen coordination with and outreach to State and local election officials on cybersecurity best practices.
- Grants for Innovations in Election Administration.—EAC is directed to assess the feasibility of establishing a competitive grant program for research and other innovative initiatives to improve election administration. Such initiatives may include (but are not limited to): combating the dissemination and public acceptance of misinformation about elections, using data analysis to evaluate the integrity of State systems, and identifying recommendations for voter registration, mail ballots, and official communications to modernize and fortify election systems. EAC is directed to brief the Committee not later than 90 days after enactment of this Act on its assessment.
The committee expresses concern about the growing amount of sensitive data the Securities and Exchange Commission (SEC) and market participants are storing:
- Data Security.—It is critically important to both investors and the U.S. capital markets that the SEC fortify its cybersecurity threat detection, response, and mitigation process. The SEC is collecting an increasing amount of market-sensitive data and PII, including through Form N–PORT and the CAT. As a repository for sensitive market data and a likely target for those who wish to manipulate U.S. markets, the security of the CAT system and data is paramount. The Committee strongly supports the SEC’s efforts to strengthen and protect its information technology systems and systems it oversees maintained by the self-regulatory organizations, including the CAT system and EDGAR (the Electronic Data Gathering, Analysis, and Retrieval system). The Committee also strongly urges the SEC, in its oversight of the Financial Industry Regulatory Authority, to ensure the CAT has adequate breach notification policies in place so affected participants are promptly notified of critical security events.
The Department of the Treasury must prioritize the cybersecurity of the financial services sector:
- Cybersecurity in the Financial Services Sector.—The National Defense Authorization Act for Fiscal Year 2021 formally codified Sector Risk Management Agencies (SRMAs), which are responsible for managing engagement between the Federal government and private-sector entities within a given critical infrastructure sector. National resilience requires that the government and private sector be able to identify, assess, and mitigate risk across national critical infrastructure in order to withstand and quickly recover from an attack. As designated SRMA for the financial services sector, the Department of the Treasury is responsible for protecting the financial services sector and its customers from the devastating effects of cyberattacks. The Committee urges continued coordination to develop consistent and workable cybersecurity safeguards across the financial services sector, including within the payment processing and financial technology industries. The Committee expects the Department to prioritize the activities of the Office of Cybersecurity and Critical Infrastructure Protection (OCCIP) to improve communication and coordination with the financial services sector. OCCIP is directed to brief the Committee, within 90 days of enactment of this Act, on its collaborative efforts with the financial services sector to enhance cybersecurity controls and safeguards, and the proposed methods and tools to improve these efforts.
The committee also directs the Department of the Treasury to address its own cybersecurity through a dramatic increase in funding::
- The Cybersecurity Enhancement Account (CEA) is a dedicated account designed to identify and support Department-wide investments for critical IT improvements, including the systems identified as High Value Assets.
- The Committee recommends $132,027,000 for the CEA. The recommendation includes $114,027,000 to support Department-wide efforts to address the impacts of the SolarWinds attack and to implement measures to minimize the impacts of such incidents in the future.
- Quarterly Reports.—Within 60 days of enactment of this Act, the Department is directed to submit a plan for the obligation of funds by quarter for each CEA investment. The plan shall include prior year unobligated balances and delineate planned obligations by source year of appropriation. The plan shall also include anticipated unobligated balances at the close of the fiscal year and the planned obligation of carryover in future years, by quarter, until all funds are obligated. Treasury is directed to submit quarterly updates on this plan.
The Department of the Treasury’s Financial Crimes Enforcement Network (FinCEN) is directed to address business email compromise in the real estate sector and some misfires of automated technology designed to fight money laundering:
- Business Email Compromise.—Email compromise fraud schemes generally entail criminal attempts to compromise the email ac- counts of victims to send fraudulent payment instructions to financial institutions or business associates in order to misappropriate funds or to assist in financial fraud. The Committee is concerned with the prevalence of such schemes in the real estate sector. FinCEN is directed to brief the Committee within 90 days of enactment of this Act on its ongoing efforts to combat and raise aware- ness of business email compromise scams, including joint activities conducted with the Department of Justice, Federal Bureau of Investigation, Federal Trade Commission, and other relevant agencies.
- Automated Technology to Combat Money Laundering.—The Committee is aware of reports of Muslim Americans whose bank accounts have been suddenly and erroneously closed due to increased scrutiny by financial institutions. The Committee supports FinCEN’s work with Federal regulators and financial institutions to encourage innovative approaches to detect and combat money laundering and terrorist financing, including the use of artificial intelligence and machine learning technology. However, the Committee is concerned that such tools may contain implicit biases that result in discrimination against individuals based on race, religion, or culture. The Anti-Money Laundering Act of 2020 contained significant revisions to existing law to strengthen anti-money laundering programs, while also taking into account the potential effects of such programs on de-risking and financial inclusion. As the new mandates are implemented, the Department and FinCEN are urged to carefully consider the disparate impact that these tools and processes may have on certain individuals and groups.
The “Agriculture, Rural Development, Food and Drug Administration, and Related Agencies Appropriations Act, 2022” (H.R.4356) funds the U.S. Department of Agriculture’s (USDA) broadband programs, notably through the Rural Utilities Service (RUS). In the committee report, for the top-line of the USDA program that funds broadband development in rural areas, the committee explained:
- For the Rural Electrification and Telecommunications Loans Program Account, the Committee provides a loan level of $7,195,000,000. In addition, the Committee provides $33,270,000 for administrative expenses.
- Consumer Oriented Operating Loans.—Rural cooperative utilities, which are owned by consumers have suffered severe energy cost spikes due to winter storm Uri and other severe weather events. The Rural Utilities Service (RUS) is encouraged to offer financially feasible low interest loans and other financial incentives to cooperatives (and other non-profit electric utilities) to smooth the impact of severe weather related energy costs and to finance consumer-oriented energy efficiency measures which would provide relief to rural consumers as well as facilitate reductions in carbon pollution.
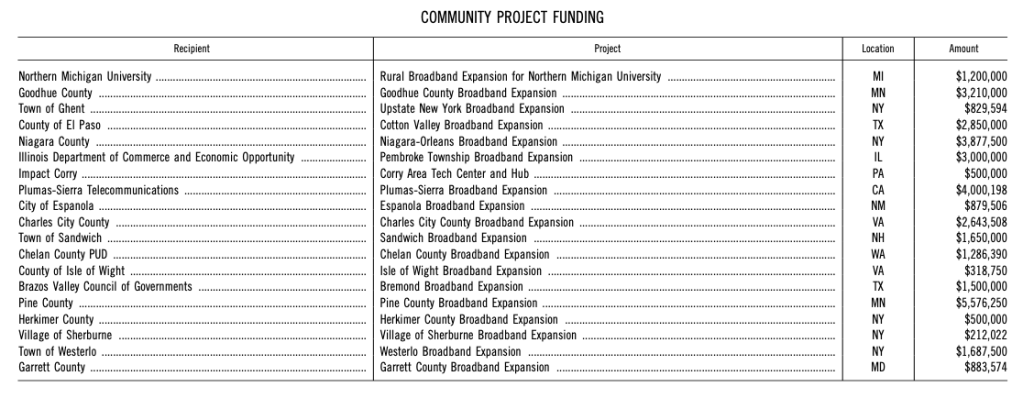
For the Broadband Program, the Committee provides an appropriation of $1,772,000 for a loan authorization level of $11,869,000. The Committee specifies the following projects and amounts to be funded in fiscal year 2022.
Earmarks returned this year (renamed “Community Project Funding,” for “That which we call a rose/by any other name would smell as sweet;” and the committee listed those broadband projects for which Members requested funds:
The committee continued:
- Broadband and Tribal Colleges and Universities.—The Committee encourages the Secretary of Agriculture to explore opportunities to expand broadband for 1994 Institutions (as defined in Sec. 532 of the Equity in Educational Land-Grant Status Act of 1994 (7 U.S.C. 301 note) under the Rural Electrification Act of 1936 (7 U.S.C. 901 et seq.). Stronger efforts are needed to support expansion and maintenance of broadband connectivity, including, but not limited to, equipment costs, maintenance of broadband systems, broadband infrastructure expansion, and ongoing broadband operations expenses directly related to 1994 Institutions broadband systems.
- Broadband Technologies.—he Committee awaits the report requested in H. Rpt. 116–646 detailing the progress of the ReConnect program, including technologies used and communities served.
- Indian Country Broadband.—The Committee urges the USDA to responsibly and efficiently take action to increase access to broadband on rural Tribal lands and supports consultation with federally recognized Indian Tribes, Alaska Native villages and corporations, and entities related to Hawaiian homelands.
- Open Access.—The Committee recognizes the value of open access broadband fiber infrastructure projects as well as the challenges these projects face in qualifying for federal funding and directs the USDA Rural Utilities Service (RUS) to support financially-feasible open access infrastructure projects that meet its program goals.
- ReConnect Program.—The Committee provides an additional $800,000,000 for the ReConnect program to increase access to broadband connectivity in unserved and underserved rural communities, targeting areas of the country with the largest broadband coverage gaps, including those with mountainous terrain.
- ReConnect Awards.—The Committee recognizes the importance of quickly closing the digital divide to economic development, especially in rural communities, and further recognizes how the COVID–19 pandemic has exacerbated existing digital disparities over the last year. Similarly, the Committee recognizes that the difficulties of operating in a pandemic can make the administration of broadband projects more difficult due to disruptions in workforce and supply chains. Therefore, the Committee encourages Rural Development to work to expeditiously disburse ReConnect funds once grants and loans are awarded. Additionally, the Committee encourages the Department to examine, and appropriately adjust and lower the collateral requirements within ReConnect Loan Agreements, Grant Agreements, or Loan/Grant Agreements to ensure greater Program access.
- ReConnect Service Areas.—RUS Telecommunications Program funds should not be awarded in any areas, study areas or census blocks where a recipient of FCC High-Cost USF support is already subject to a buildout obligation of 25/3 Mbps or greater for fixed terrestrial broadband, except that RUS Telecommunication Program funds may be awarded in such areas to help finance construction of the network. This shall not apply in cases where the FCC has not provided for final approval of an award of such funds.
The “Energy and Water Development and Related Agencies Appropriations Act, 2022” (H.R.4549) funds the Department of Energy (DOE) and its various programs to help the cybersecurity of the U.S. electric grid and other energy programs. The committee report explains a number of these programs and what the committee wants to see in the coming fiscal year:
- Benefits of Renewable and Clean Energy Technologies.—The Committee recognizes the significant impacts of the nation’s energy infrastructure on social, health, economic, and ecological outcomes, and that successful decarbonization efforts must consider these im- pacts in a holistic manner. Therefore, the Department is encouraged to expand its efforts to study the varied benefits of distributed, renewable, and clean energy technologies, including their potential to 1) address racial and economic inequality; 2) promote community health and well-being; 3) strengthen the climate and disaster resilience and cybersecurity of the nation’s energy infra- structure; and 4) increase democratic participation in the energy sector. Further, the Department is encouraged to examine how in- creased public and nonprofit ownership of distributed, renewable, or clean energy infrastructure, including federal, regional, municipal, and cooperative ownership of generation, distribution, and transmission, can employ accountability mechanisms to maximize the achievement of the described benefits, while also increasing planning capacity to accelerate the transition to a net-zero emissions economy. Finally, to conduct interdisciplinary research on these questions, the Department is encouraged to collaborate with other federal agencies, such as the Department of Health and Human Services, Department of Labor, Department of Commerce, Environmental Protection Agency, Department of the Interior, and Department of Homeland Security, including the Cybersecurity and Infrastructure Security Agency.
- Blockchain for Energy Procurement and Traceability.—Public, open-source decentralized technologies like blockchain are being used in various markets worldwide to develop new digital plat- forms for renewable energy procurement and help the companies, cities, and other renewable energy buyers meet their voluntary procurement goals. These digital solutions built with decentralized technologies may help simplify, reduce costs, and enhance the traceability of renewable energy trading and reporting among market participants. These solutions may also help expand access to more market participants. The Department is directed to coordinate research about the opportunity and needs for new digital solutions built with public, open-source decentralized technologies to promote renewable energy procurement, market access, and market growth.
- Development of Open-Source Technology Services for Clean Energy Products and Services.—The Committee notes the growing global competition for clean energy goods and services as well as the need to support energy sector digitalization. There is an opportunity to position American goods and services ahead of global com- petition by developing and implementing open-source technology standards for renewable energy, storage, energy efficiency, electric vehicle, and other clean energy technologies so that these goods and related services deliver their full economic potential. The Department is encouraged to coordinate research evaluating and testing open-source technological standards for clean energy products and services, particularly in terms of use of digital identities and decentralized identity registries for such goods, that promote great- er interoperability and market access across energy markets and, ultimately, help position the United States as a clean energy solutions leader.
The DOE’s Cybersecurity, Energy Security, and Emergency Response (CESER) program would receive $177 million, some $24 million less than the Biden Administration requested but $21 million more than its FY 2021 funding. The committee has a number of policy directions to CESER:
- The Cybersecurity, Energy Security, and Emergency Response program leads the Department’s efforts to secure the nation’s energy infrastructure against all hazards, reduce the risks of and impacts from cyber events and other disruptive events, and assist with restoration activities. A reliable and resilient power grid is critical to the nation’s economic competitiveness and leadership.
- Additional direction related to Department-wide crosscutting initiatives is provided under the heading Crosscutting Initiatives in the front matter of Department of Energy.
- The Department is directed to include an itemization of funding levels below the control point in future budget submissions.
- The nation continues to face global cybersecurity threats from nations such as Iran, Russia, and North Korea that have launched documented cyberattacks on the country. Because of their unique location and geography, island states and territories host a disproportionate amount of our national security and defense forces, putting island states and territories and the electric grid infrastructure at risk. Remote island communities also face the added burden of not being able to integrate with mainland infrastructure and are excluded from designations and programs such as the Defense Critical Electrical Infrastructure, which may otherwise afford these communities with additional resources. The Committee encourages the Department to work with electric cooperatives, public utility districts, investor-owned utilities, and municipal utilities serving island communities to plan and build out needed cybersecurity infrastructure. The Department is directed to submit to the Committee not later than 180 days after enactment of this Act a report assessing the current vulnerabilities of island communities and how the Department can provide resources and technical assistance to mitigate vulnerabilities.
- In light of documented cyber targeting of utilities, including by state actors, the Committee encourages the Department to incorporate pilot programs with private sector participants to demonstrate active defense cybersecurity protection.
- The Committee is concerned about the substantial and growing threat from cybersecurity attacks to the electrical grid. The Committee supports the Department’s efforts to identify and develop defenses for these new cyber threats, including developing proof of concept algorithms that can be tested across a full range of attacks in both testbed and real environments. The recommendation provides not less than $2,000,000 for digital twin projects to enable essential collaborator participation and their integration into the effort.
- The recommendation provides up to $20,000,000 for the Cyber Testing for Resilient Industrial Control System (CyTRICS) program.
- Risk Management Technology and Tools.—The recommendation provides up to $10,000,000 for consequence-driven cyber-informed engineering and $4,000,000 for university-based research and development of scalable cyber-physical platforms for resilient and secure electric power systems that are flexible, modular, self-healing, and autonomous. This activity should be conducted in coordination with the Office of Electricity.
- The recommendation provides not less than $5,000,000 to conduct a demonstration program of innovative technologies, such as technologies for monitoring vegetation management, to improve grid resiliency from wildfires.
- The recommendation includes not less than $2,000,000 to continue the establishment of a network of university-based, regional energy cybersecurity centers. The centers should address interrelated research and development challenges of cybersecurity and critical energy infrastructure and develop a trained, globally competitive workforce. The centers should be distributed regionally across the country to leverage regional utilities, national laboratories, and regulatory bodies and take into account the distinctive characteristics of each region’s electricity system, network of oil and gas infrastructure, and workforce expertise. The Department is directed to coordinate these activities with the Office of Electricity and the Office of Energy Efficiency and Renewable Energy.
- Response and Restoration.—The Committee places a high priority on ensuring the protection of the electric grid against cyberattacks and extreme weather events. The Response and Restoration pro- gram coordinates a national effort to secure the U.S. energy infra- structure against all hazards, reduce impacts from disruptive events, and assist industry with restoration efforts. The program delivers a range of capabilities including energy sector emergency response and recovery, including emergency response of a cyber nature; near-real-time situational awareness and information sharing about the status of the energy systems to improve risk management; and analysis of evolving threats and hazards to energy infra- structure.
- Information Sharing, Partnerships, and Exercises.—The Information Sharing, Partnerships, and Exercises program supports energy sector security and resilience through coordination with government and industry partners. This program provides technical assistance that incorporates exercises to strengthen federal, regional, state, tribal, and territorial abilities to work together to prepare for and mitigate the effects of an energy sector emergency and focuses on training the next generation workforce on energy sector risks.
The “Department of the Interior, Environment, and Related Agencies Appropriations Act, 2022” (H.R.4372) contains a funding increase for cybersecurity. The Environmental Protection Agency (EPA) would receive a massive boost in cybersecurity funding on a percentage basis as part of a larger trend this year, quite likely because the spate of successful penetrations of U.S. government systems by Russian and Chinese hackers:
- Homeland Security.—The Committee recommends $40,388,000, $4,655,000 above the enacted level and equal to the request. The Committee is aware of reports of cyber intrusions into critical water infrastructure and notes the continuing vulnerability of the water sector to cyberthreats. The Agency is directed to periodically brief the Committee on the actions it is taking to protect against this and other threats.
Of course, the EPA funding bump is due to an attack on a Florida drinking water system earlier this year.
The ”Departments of Labor, Health and Human Services, and Education, and Related Agencies Appropriations Act, 2022” (H.R.4502) and its committee report contain some technology items. The Department of Health and Human Services (HHS) would get a significant increase in funding, but the committee tells the agency to shutter an existing program so as to avoid duplication:
- The Committee provides $159,116,000, an increase of $101,296,000, for information technology cybersecurity in the Office of the Chief Information Officer and HHS-wide to strengthen the Department’s cybersecurity posture. The Committee does not include funding to continue HHS Protect, as capabilities shall no longer be duplicated at the Departmental level or shall be delegated to the appropriate operating division.
The National Institutes of Health (NIH) would also see a significant funding increase to aid its cybersecurity:
- Cybersecurity.—The Committee includes an increase of $100,000,000 to support expanded cybersecurity efforts at NIH, as requested in the fiscal year 2022 budget. Funding will enhance Security Operations Center functions, expand threat mitigation and incident response capabilities, implement important architectural improvements to the NIH network, and implement tools and technologies to allow real time monitoring of activity across a variety of sources.
The committee tasks the Secretary of Health and Human Services with examining and reporting on the effect of social media “and negative social and individual outcomes:”
- Report on the Effects of Social Media Use.—The Committee continues to support efforts by the Secretary to investigate whether there is a relationship between the use of social media and negative social and individual outcomes, including clinical and undiagnosed depression; self-harm, such as suicide, attempted suicide, and suicidal ideation; harm to others; cyber bullying; chronic anxiety; or social isolation. Such investigation should consider the role of content and presentation in social media that is linked to negative outcomes, as well as the design of algorithms to prioritize user engagement. In addition, the report should include consideration of the following questions: what type of content drives user participation on these platforms; how is that content most frequently presented to users on these platforms; and does that presentation lead to negative physical, mental or emotional health outcomes; what types of emotions characterize social media interactions; how do these companies design their algorithms to engage users; and is that design prioritizing engagement over user well-being. The Committee encourages the Secretary to provide a report within 90 days of enactment of this Act on the continued progress in this research area.
Even the bill that funds Congress has technology provisions. The “Legislative Branch Appropriations Act, 2022” (H.R.4346) requires the following as directed by the committee report:
- The Committee is concerned that many legislative branch agencies continue to store critical data on Capitol Hill and in the Alternate Computing Facility which does not meet high physical security standards or Tier III data center requirements and has had a history of system failures and outages. The Committee directs each legislative branch agency to utilize available contract vehicles to expeditiously secure agency data in facilities that have been third-party certified to meet Tier III standards and geographically located outside of the National Capitol Region (NCR). Additionally, the Committee directs each legislative branch agency to provide the Committees an action plan within 60 days of enactment of this Act which details a schedule, cost and implementation plan to secure agency data in a certified Tier III facility by January 31, 2022.
- Cloud Technologies: The Chief Administrative Officer (CAO) is encouraged to continue to investigate and pilot various cloud service options that will provide House offices with greater accessibility to their files, enhanced collaboration tools, and more storage. The Committee supports standardizing cloud services to strengthen the House’s security posture and provide Member offices additional support and cost savings.
- Combatting Cyberattacks: The Committee notes that the CAO is charged with combatting cyberattacks that could disrupt the House’s ability to perform its constitutional duties. Accordingly, the recommendation includes funding in fiscal year 2022 to continue to strengthen cyber defenses from sophisticated actors and encourages the CAO to explore a Zero Trust security model based on the National Institute of Standards and Technology standards as one of the tools to use against novel threat actors.
- Digital Workspace Technologies: The Committee recognizes that the use of digital workspace technologies in Member offices can increase user productivity, enhance cybersecurity, and allow workforce flexibility for both Congressional staff and Members of Congress. The Committee continues to encourage the exploration of multi-factor authentication solutions to strengthen the cybersecurity posture of all legislative offices, including strategies and programs that reduce the total life cycle costs of traditional legacy workspace infrastructure.
The committee included increased funding for two Congressional agencies to give the body better understanding of and insight into technology issues:
- The Committee notes the interest among some Members during the past several years to reinstitute the Office of Technology Assessment (OTA), which was defunded in 1995. In fiscal year 2019 the Committee instructed the National Academy of Public Administration (NAPA) to conduct a study to determine the best way to increase Congress’s access to needed in-depth analysis of fast-breaking technology developments. The NAPA report, released in November, 2019, recommended strengthening the capacity of the Government Accountability Office (GAO) and Congressional Research Service (CRS) in technology assessment rather than restarting OTA. The Committee is pleased with both CRS and the GAO’s efforts to increase the depth and breadth of its capacity to provide research and policy analysis on current and emerging legislative issues related to science and technology (S&T) and Federal uses and oversight of S&T.
- CRS is encouraged to continue to hire additional staff for their specialized teams working on science and technology issues expanding its capacity and expertise to allow CRS to meet the growing need of Congress for timely, complex, and multidisciplinary analysis of policy issues related to these rapidly changing technologies, the effects of Federal government in oversight of such technologies, and the effects of the Federal government S&T policies across all sectors. CRS is also encouraged to increase outreach efforts to make Members and congressional staff more aware of the resources it provides related to S&T issues Congress is examining.
- Additionally, in 2019 the GAO established a Science, Technology Assessment, and Analytics (STAA) team to better address the evolving and time-sensitive needs of Congress. The Committee encourages the GAO to continue to strengthen its STAA S&T team and the Innovation Lab to increase the depth, breadth, and diversity of knowledge available to meet congressional needs.
- As a result, the bill provides the full request for CRS and GAO to strengthen S&I programs. The Committee will continue to review the work of CRS and the GAO to see if other steps are needed in the future.
The committee had many directions and requirements for the Department of Veterans Affairs’ (VA) troubled Electronic Health Record Modernization in the “Military Construction, Veterans Affairs, and Related Agencies Appropriations Act, 2022” (H.R.4355) and the committee report:
- VA Electronic Health Record Modernization (EHRM).—After at least a decade of Congressional encouragement to DOD and VA to develop a single electronic health record (EHR), VA finalized a contract in 2018 to acquire the same EHR system that DOD is adopting. The bill includes $2,637,000,000 for EHRM and continues strict quarterly reporting of timelines, performance milestones, costs, implementation, and change management. The bill also continues the requirement for GAO to review EHRM implementation so that Congress can be informed of any problems at a point where they can be promptly and economically addressed.
- The Veterans Electronic Health Record is a unified account designed to manage the effort to develop an interoperable electronic health record system that will access seamlessly the records of Veterans in the VA system and those of the Department of Defense and of community providers. The VA system is the same as the one chosen by DOD and is planned to be rolled out with the same timeline and geographic areas as DOD in order to realize cost efficiency savings.
- The bill provides an increase of $10,000,000 above the fiscal year 2021 level to support VA’s on-going efforts to deploy the new electronic health record system. Within the total funding, the bill includes $1,416,498,000 for the electronic health record contract, $276,705,000 for program management, and $943,797,000 for infra- structure support. Funding is made available for three years due to the uncertainty of the timing of obligations for this substantial effort.
- This account is intended to be the single source of funding within VA for the electronic health record effort. No authority is provided for funds from other VA accounts to be transferred into this account nor for funds from this account to be transferred out to other accounts. Consistent with the effort to centralize financial management of the development of the electronic health record, the Committee continues to direct the Department to manage this effort at the headquarters level in the Office of the Deputy Secretary.
- The bill continues language requiring the Secretary to submit a quarterly report to the Committees on Appropriations of both Houses of Congress detailing obligations, expenditures, and deployment strategy by facility. VA is directed to continue quarterly briefings on performance milestones, costs, and changes to implementation and management plans, and to provide an accurate up-to-date deployment schedule each quarterly briefing. Additionally, the Committee directs the Department to provide updates on plans and efforts to integrate community care providers into the new EHR system. Such updates should be submitted concurrently with the quarterly reports.
- In addition, bill language is included requiring notice to and approval from the Committees on Appropriations of both Houses of Congress on any changes to the deployment schedule. Should there be any deviation from the deployment schedule, the Committee directs the Department to formally submit in writing a proposed up- dated deployment schedule within 7 days of notification to the Committees of any potential Change, and prior to implementation of the updated deployment schedule. The Committee repeats the fiscal year 2020 directive for GAO to perform quarterly performance reviews of the VA electronic health record deployment. It is expected that this quarterly reporting will provide the Committees and VA with timely information to properly oversee this effort and address important issues.
- Cybersecurity for Electronic Health Records and Blockchain Technology.—Recognizing the ongoing challenges of sharing data between MHS GENESIS and the Department’s EHRM initiative, the Committee encourages the Department to continue prioritizing efforts to protect Veterans’ sensitive information when implementing EHRM, and recommends the Department consider emerging technologies, such as blockchain technology, if future requirements drive a need to modify VA’s security architecture and technical solutions. The Committee understands that the Department is undertaking a pilot to study the use of blockchain technology to share data and looks forward to the results of the pilot being shared with the Committee.
- Transparency on EHRM Third-Party Application Review.—The Committee continues to encourage VA to ensure that the new EHRM initiative provides an open architecture that allows a governance and oversight process for administering access and support to deploy third-party applications, components, and application programming interfaces. The Committee encourages the Department and the Federal Electronic Health Record Modernization Program Office to ensure the standards and evaluation criteria for commercially available software, tools and products that advance interoperability and seamless care are readily available for review, such as on the EHRM webpage.
The committee also weighed in on the security of telehealth communications:
- Encrypted Communications for Telehealth.—In coordination with the Veterans Health Administration and Office of Electronic Health Records Modernization, the Office of Information Technology is directed to utilize the best technologies, such as end-to-end encrypted communications with zero-trust architecture, that can reliably serve Veterans and healthcare providers.
© Michael Kans, Michael Kans Blog and michaelkans.blog, 2019-2021. Unauthorized use and/or duplication of this material without express and written permission from this site’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to Michael Kans, Michael Kans Blog, and michaelkans.blog with appropriate and specific direction to the original content.
Photo by Alexandre Debiève on Unsplash