Subscribe to my newsletter, The Wavelength, if you want updates on global technology developments four times a week.
Other Developments

- At its first monthly meeting in decades, the Federal Trade Commission (FTC) undertook a number of significant actions in party line votes with the three Democratic Commissioners voting for the items, including:
- Section 18 Rulemaking Procedures: In a 3-2 vote, the Commission approved streamlining the procedures for Section 18 rules prohibiting unfair or deceptive acts or practices. Section 18 rules allow the Commission to seek redress for defrauded consumers and penalties against firms that cheat.
- The Federal Trade Commission approved changes to its Rules of Practice to modernize the way it issues Trade Regulation Rules under Section 18 of the FTC Act, which will provide a roadmap for businesses, stop widespread consumer harm, and promote robust competition.
- These changes bring agency procedures back in line with the 1975 statute that granted the agency Section 18 rulemaking authority, and they build on the agency’s announcement earlier this year of a Rulemaking Group within the office of the General Counsel. Commissioner Rebecca Kelly Slaughter was joined by FTC Chair Lina Khan and Commissioner Rohit Chopra in a statement, noting the changes will reinvigorate the FTC’s rulemaking procedures and vastly improve the Commission’s work on behalf of consumers and small businesses.
- Recently, the Supreme Court ruled that courts can no longer award refunds to consumers in FTC cases brought under Section 13(b) of the FTC Act, reversing four decades of case law that the Commission has used to provide billions of dollars of refunds to harmed consumers. In light of that decision, pursuing violations of Trade Regulation Rules – also referred to as the Magnuson-Moss Rules – will allow the Commission to seek redress, damages, penalties, and other relief from wrongdoers.
- The amendments make changes to the Commission’s procedure for initiating rulemaking proceedings, and the process by which members of the public can seek an informal hearing in a rulemaking. For example, under the revised rules, informal hearing procedures make it easier for stakeholders to participate. Other changes include elimination of requirements in the current rules that are not mandated by the FTC Act, including publication of a staff report containing an analysis of the rulemaking record and recommendations as to the form of the final rule for public comment. The rulemaking procedures build in extensive opportunities for public input, far in excess of the opportunities for public comment under the Administrative Procedure Act.
- “Statement of Enforcement Principles Regarding ‘Unfair Methods of Competition’ Under Section 5 of the FTC Act” (2015): In a 3-2 vote, the Commission rescinded the policy statement issued by the Commission in 2015 in order to better align with the requirements set out by Congress to condemn “unfair methods of competition.”
- Congress directed the FTC to enforce the prohibition on “unfair methods of competition.” This prohibition extends beyond the Sherman Act and the Clayton Act. The 2015 Policy Statement purported to establish an analytical framework on how the Commission would seek to enforce the prohibition.
- Chair Lina M. Khan was joined by Commissioners Rebecca Kelly Slaughter and Rohit Chopra in a statement, which noted that the 2015 policy was shortsighted, and that the Commission must follow the congressional mandate to condemn “unfair methods of competition.” They explained that “[i]n practice, the Statement has doubled down on the Commission’s longstanding failure to investigate and pursue ‘unfair methods of competition.’” Rescinding the statement, they concluded, is crucial to bringing the FTC back in line with its statutory obligations.
- The Commission’s inability, after a century of commanding this statutory authority, to deliver clear Section 5 principles suggests that the time is right for the Commission to rethink its approach and to recommit to its mandate to police unfair methods of competition even if they are outside the ambit of the Sherman or Clayton Acts. The task will require careful and serious work, but it is one that our enabling statute expected and required.”
- The majority statement also noted that the Commission will exercise this authority consistent with congressional directives and appropriate case law. In addition, the Commission may consider additional guidance, policy statements, and rules describing conduct that may violate the prohibition on unfair methods of competition.
- Made in the USA Rule: In a 3-2 vote, the Commission finalized the Made in the USA Rule. The rule will help ensure that consumers can confidently buy American, and that honest companies can realize the benefits of the Made in USA label.
- Enforcement Investigations: In a 3-2 vote, the Commission approved a series of resolutions that will streamline investigations by Commission staff into specific industries or specific conduct. Priority targets include repeat offenders; technology companies and digital platforms; and healthcare businesses such as pharmaceutical companies, pharmacy benefits managers, and hospitals. The agency is also prioritizing investigations into harms against workers and small businesses, along with harms related to the COVID-19 pandemic. Finally, at a time when merger filings are surging, the resolutions will allow the Commission to ramping up enforcement against illegal mergers, both proposed and consummated.
- The Federal Trade Commission voted to approve a series of resolutions authorizing investigations into key law enforcement priorities for the next decade. Specifically, the resolutions direct agency staff to use “compulsory process,” such as subpoenas, to investigate seven specific enforcement priorities. Priority targets include repeat offenders; technology companies and digital platforms; and healthcare businesses such as pharmaceutical companies, pharmacy benefits managers, and hospitals. The agency is also prioritizing investigations into harms against workers and small businesses, along with harms related to the COVID-19 pandemic. Finally, at a time when merger filings are surging, the agency is ramping up enforcement against illegal mergers, both proposed and consummated.
- In remarks delivered during the open meeting, Chair Lina M. Khan noted that the resolutions approved today represent an important step in rethinking the work of the FTC. Instituting new cross-agency, investigatory resolutions will promote a more holistic use of the FTC’s enforcement authorities to stop bad actors across markets.
- Compulsory process refers to the issuance of demands for documents and testimony, through the use of civil investigative demands and subpoena. The FTC Act authorizes the Commission to use compulsory process in its investigations. Compulsory process requires the recipient to produce information, and these orders are enforceable by courts. The Commission has routinely adopted compulsory process resolutions on a wide range of topics. Many of these resolutions cover specific industries, like the automobile industry or the postsecondary education industry, while others involve business practices that cut across sectors, like privacy or the targeting of older Americans.
- The actions taken today will broaden the ability for FTC investigators and prosecutors to obtain evidence in critical investigations on key areas where the FTC’s work can make the most impact. Each omnibus authorizes investigations into any competition or consumer protection conduct violations under the FTC Act. The omnibuses will also allow staff to use compulsory process to investigate both proposed mergers and consummated mergers. Individual Commissioners will continue to be required to sign compulsory process documents prior to issuance. With these in place, the FTC can better utilize its limited resources and move forward in earnest to fix the market structures that allow the worst predators to proliferate.
- Section 18 Rulemaking Procedures: In a 3-2 vote, the Commission approved streamlining the procedures for Section 18 rules prohibiting unfair or deceptive acts or practices. Section 18 rules allow the Commission to seek redress for defrauded consumers and penalties against firms that cheat.
- The Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) offered guidance to managed service providers (MSPs) affected by “supply-chain ransomware attack leveraging a vulnerability in Kaseya VSA software:”
- CISA and FBI recommend affected MSPs:
- Download the Kaseya VSA Detection Tool
- This tool analyzes a system (either VSA server or managed endpoint) and determines whether any indicators of compromise (IOCs) are present.
- Enable and enforce multi-factor authentication (MFA) on every single account that is under the control of the organization, and—to the maximum extent possible—enable and enforce MFA for customer-facing services.
- Implement allowlisting to limit communication with remote monitoring and management (RMM) capabilities to known IP address pairs, and/or
- Place administrative interfaces of RMM behind a virtual private network (VPN) or a firewall on a dedicated administrative network.
- CISA and FBI recommend MSP customers affected by this attack take immediate action to implement the following cybersecurity best practices. Note: these actions are especially important for MSP customers who do not currently have their RMM service running due to the Kaseya attack.
- CISA and FBI recommend affected MSP customers:
- Ensure backups are up to date and stored in an easily retrievable location that is air-gapped from the organizational network;
- Revert to a manual patch management process that follows vendor remediation guidance, including the installation of new patches as soon as they become available;
- Implement:
- Multi-factor authentication; and
- Principle of least privilege on key network resources admin accounts.
- CISA and FBI recommend affected MSPs:
- In Connecticut, HB 6607 was signed into law that will provide legal protection for many firms in the event they suffer a data breach if they happen to have been using approved cybersecurity standards. In a summary, it was explained:
- This bill prohibits the Superior Court from assessing punitive damages against a covered entity (see below) for a data breach of personal or restricted information if the covered entity meets specified cybersecurity requirements.
- Specifically, when a civil action alleges that a data breach resulted from a covered entity’s failure to implement reasonable cybersecurity controls, the court may not assess punitive damages if the covered entity created, maintained, and complied with a written cybersecurity program containing administrative, technical, and physical safeguards for protecting personal or restricted information. To qualify for this protection, these cybersecurity programs must (1) meet specified design requirements and (2) conform to an industry-recognized cybersecurity framework. However, the protection does not apply if the covered entity’s failure to implement reasonable cybersecurity controls resulted from gross negligence or willful or wanton conduct.
- Under the bill, “covered entities” are businesses accessing, maintaining, communicating, or processing personal or restricted information in or through systems, networks, or services located inside or outside the state.
- Among the enumerated cybersecurity standards covered entities in Connecticut must adhere to are:
- National Institute of Standards and Technology’s (NIST)
- Framework for Improving Critical Infrastructure Cybersecurity
- Special Publication (SP) 800-171
- SP 800-53 and 800-53a
- The Federal Risk and Management Program’s FedRAMP Security Assessment Framework
- The Center for Internet Security’s Critical Security Controls for Effective Cyber Defense
- International Organization for Standardization and the International Electrotechnical Commission’s ISO/IEC 27000-series
- The security requirements of the Health Insurance Portability and Accountability Act of 1996
- The security requirements of the Health Information Technology for Economic and Clinical Health Act
- Title V of the Gramm-Leach-Bliley Act
- Federal Information Security Modernization Act of 2014
- National Institute of Standards and Technology’s (NIST)
- The European Union Agency for Cybersecurity (ENISA) issued a report on cybersecurity for small and medium sized businesses (SME). ENISA claimed:
- The report Cybersecurity for SMEs ENISA issues today provides advice for SMEs to successfully cope with cybersecurity challenges, particularly those resulting from the COVID-19 pandemic. With the current crisis, traditional businesses had to resort to technologies such as QR codes or contactless payments they had never used before. Although SMEs have turned to such new technologies to maintain their business, they often failed to increase their security in relation to these new systems. Research and real-life experience show that well prepared organisations deal with cyber incidents in a much more efficient way than those failing to plan or lacking the capabilities they need to address cyber threats correctly.
- The report unveils the following challenges SMEs are faced with:
- Low awareness of cyber threats;
- Inadequate protection for critical and sensitive information;
- Lack of budget to cover costs incurred for implementing cybersecurity measures;
- Availability of ICT cybersecurity expertise and personnel;
- Absence of suitable guidelines tailored to the SMEs sector;
- Moving online;
- Low management support.
- ENISA made recommendations that fall into three categories:
- People
- People play an essential role in the cybersecurity ecosystem. The report draws attention to the importance of responsibility, employee buy-in and awareness, cybersecurity training and cybersecurity policies as well as third party management in relation to confidential and/or sensitive information.
- Processes
- Monitoring internal business processes include performing audits, incident planning and response, passwords, software patches and data protection.
- Technical
- At the technical level, a number of aspects should be considered in relation to network security, anti-virus, encryption, security monitoring, physical security and the securing of backups.
- ENISA added:
- In addition to the report, ENISA also publishes today the Cybersecurity Guide for SMEs: “12 steps to securing your business”. The short cybersecurity guide provides SMEs with practical high-level actions to better secure their systems, hence their businesses.
- The United States (U.S.) Government Accountability Office (GAO) assessed how well the Department of Health and Human Services (HHS) is discharging its cybersecurity duties. The GAO asserted:
- The Department of Health and Human Services’ (HHS) Office of Information Security is responsible for managing department-wide cybersecurity. HHS clearly defined responsibilities for the divisions within that office to , among other things, document and implement a cybersecurity program, as required by the Federal Information Security Modernization Act of 2014.
- For healthcare and public health critical infrastructure sector cybersecurity, HHS also defined responsibilities for five HHS entities. Among these entities are the Health Sector Cybersecurity Coordination Center, which was established to improve cybersecurity information sharing in the sector, and the Healthcare Threat Operations Center, a federal interagency program co-led by HHS and focused on, among other things, providing descriptive and actionable cyber data. Private-sector partners that receive information provided by the Health Sector Cybersecurity Coordination Center informed GAO that they could benefit from receiving more actionable threat information. However, this center does not routinely receive such information from the Healthcare Threat Operations Center, and therefore is not positioned to provide it to sector partners. This lack of sharing is due, in part, to HHS not describing coordination between the two entities in procedures defining their responsibilities for cybersecurity information sharing. Until HHS formalizes coordination for the two entities, they will continue to miss an opportunity to strengthen information sharing with sector partners.
- Further, HHS entities led, or participated in , seven collaborative groups that focused on cybersecurity in the department and healthcare and public health sector. These entities regularly collaborated on cyber response efforts and provided cybersecurity information, guidance, and resources through these groups and other means during COVID-19 between March 2020 and December 2020. In addition, the HHS entities coordinated with the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) to address cyber threats associated with COVID-19. Further, the HHS entities fully demonstrated consistency with four of the seven leading collaboration practices that GAO identified, and partially addressed the remaining three (see table). Until HHS takes action to fully demonstrate the remaining three leading practices, it cannot ensure that it is improving cybersecurity within the department and the healthcare and public health sector.
- The GAO made seven recommendations to HHS:
- The Secretary of HHS should direct the Chief Information Officer to coordinate cybersecurity information sharing between the Health Sector Cybersecurity Coordination Center and Healthcare Threat Operations Center. (Recommendation 1)
- The Secretary of HHS should direct the Chief Information Officer to monitor, evaluate, and report on the progress and performance of the HHS Chief Information Security Officer Council, Continuous Monitoring and Risk Scoring Working Group, and Cloud Security Working Group. (Recommendation 2)
- The Secretary of HHS should direct the Assistant Secretary for Preparedness and Response to monitor, evaluate, and report on the progress and performance of the Government Coordinating Council’s Cybersecurity Working Group and HHS Cybersecurity Working Group. (Recommendation 3)
- The Secretary of HHS should direct the Chief Information Officer to regularly monitor and update written agreements describing how the HHS Chief Information Security Officer Council, Continuous Monitoring and Risk Scoring Working Group, and Cloud Security Working Group will facilitate collaboration, and ensure that authorizing officials review and approve the updated agreements. (Recommendation 4)
- The Secretary of HHS should direct the Assistant Secretary for Preparedness and Response to ensure that authorizing officials review and approve the charter describing how the HHS Cybersecurity Working Group will facilitate collaboration. (Recommendation 5)
- The Secretary of HHS should direct the Assistant Secretary for Preparedness and Response to (1) finalize written agreements that include a description of how the Government Coordinating Council’s Cybersecurity Working Group will collaborate, (2) identify the roles and responsibilities of the working group, (3) monitor and update the written agreements on a regular basis, and (4) ensure that authorizing officials leading the working group approve the finalized agreements. (Recommendation 6)
- The Secretary of HHS should direct the Assistant Secretary for Preparedness and Response to update the charter for the Joint Healthcare and Public Health Cybersecurity Working Group for the current fiscal year and ensure that authorizing officials leading the working group review and approve the updated charter. (Recommendation 7)
- The chairs and ranking members of the House and Senate subcommittees with jurisdiction over antitrust and competition matters wrote Federal Trade Commission (FTC) Chair Lina Khan “urging the FTC to continue its efforts to hold Facebook accountable for violations of antitrust laws and pursue its monopolization case against the company…after a federal judge dismissed antitrust complaints brought against Facebook by the FTC and more than 40 states earlier this week.” The Senate Judiciary Committee’s Competition Policy, Antitrust, and Consumer Rights Subcommittee Chair Amy Klobuchar (D-MN) and Ranking Member Mike Lee (R-UT) and the House Judiciary Committee’s Antitrust, Commercial, and Administrative Law Subcommittee Chair David Cicilline (D-RI) and Ranking Member Ken Buck (R-CO) stated:
- The conduct alleged in the FTC’s complaint against Facebook raised serious competitive concerns. Claims that Facebook acquired Instagram and WhatsApp to prevent them from emerging as competitive rivals and that it blocked rival applications from interoperating with Facebook’s systems to prevent them from growing into serious competitors are deeply troubling. As the Judge himself noted, the federal antitrust agencies rarely bring antitrust cases against Big Tech — an approach that has resulted in the overwhelming consolidation of power in the hands of a few digital platforms, including Facebook.
- Accordingly, it is essential that the Commission take action to deter anticompetitive conduct by digital monopolists by ensuring that they are held liable for antitrust violations to the full extent of the law. Competition and innovation in America’s digital economy depend on it. That is why we support providing additional resources for antitrust enforcement and why each of us has proposed legislation to strengthen the antitrust laws.
- As Slovenia takes over the Presidency of the Council of the European Union from Portugal, it has issued its program of policy items it intends to pursue until France takes over in January 2022. Among other items, in a summary, Slovenia stressed the following:
- The COVID-19 pandemic, during which life and work have moved online, has increased our vulnerability to cyberattacks. That is why we will focus our efforts on strengthening European cyber resilience. More needs to be done in order for us to be better prepared and to be able to respond in a coordinated manner to potential large-scale cyberattacks.
- At the same time, we must ensure a lasting recovery in all sectors of the economy and public life. To mitigate the socio-economic consequences of the COVID-19 pandemic, one of the priorities of the Slovenian Presidency will be the effective implementation of the Next Generation EU instrument and the Recovery and Resilience Facility, with the aim of facilitating the adoption of national recovery plans as soon as possible. It is our wish to make the most of the implementation of these two instruments to accelerate the green and digital transition, which will create jobs, strengthen the resilience of our societies and ensure the health of our environment.
- Digital transformation was one of the EU’s objectives even before the pandemic, an event that has only further accelerated this process. Digital technologies have become essential for working, doing business, learning, socialising and accessing everything from health services to culture. Since the applicable legislation no longer satisfactorily addresses current challenges, progress needs to be made on digital services and markets in order for the EU to set new standards in the use of digital platforms.
- We will strive for the digital sovereignty of Europe and the ethical use and development of artificial intelligence, which, in connection with the availability of big data, is being identified as one of the key technologies of the future.
- The United Kingdom’s Information Commissioner’s Office (ICO) “has launched a suite of lesson plans and worksheets aimed at teaching primary and secondary school pupils how to protect their privacy online and how they can control what online companies and platforms know about them” per their press release. The ICO added:
- The resources explain what counts as personal data, how to protect it and how to keep it private on social media. They cover the curriculum in all parts of the UK and can be downloaded for free from the ICO website.
- The resources form part of the ICO’s work on building awareness of the Children’s Code, a set of standards that online services must follow if they are likely to be accessed by children. That includes putting in place extra layers of protection for children’s data.
- The ICO will be producing more resources around the principles of the Children’s Code to ensure that young people know what to expect when they open an app, visit a website or play an online game.
- The National Institute of Standards and Technology (NIST) is making available Draft NISTIR 8286A, Identifying and Estimating Cybersecurity Risk for Enterprise Risk Management (ERM) for a second round of comments. NIST explained:
- This report provides a more in-depth discussion of the concepts introduced in NISTIR 8286, Integrating Cybersecurity and Enterprise Risk Management (ERM). This IR8286 series document is intended to help organizations better implement cybersecurity risk management (CSRM) as an integral part of ERM – both taking its direction from ERM and informing it. The increasing frequency, creativity, and severity of cybersecurity attacks mean that all enterprises should ensure that cybersecurity risk is receiving appropriate attention within their ERM programs and that the CSRM program is anchored within the context of ERM.
- This second draft specifically incorporates feedback received during the first public comment period and provides improved editorial updates and graphics to better illustrate the intersection of cybersecurity and enterprise risk management. With the inclusion of an example risk detail report (RDR) template, this draft more clearly demonstrates how risks are summarized in the risk register using methods for populating the RDR. The language surrounding activities – including metrics and communication at each level of the enterprise – has also been updated, and the topics of privacy and supply chain have been introduced for planned future treatment.
- A companion document, NISTIR 8286B: Prioritizing Cybersecurity Risk for Enterprise Risk Management, will be available for review and comment in the coming weeks.
- New Zealand’s government “has agreed to establish a consumer data right framework for New Zealand.” The government contended:
- On 5 July 2021, the Government decided to implement a new legislative framework for a consumer data right. This will allow consumers to securely share data that is held about them with trusted third parties, using standardised data formats and interfaces.
- The consumer data right will be rolled out on a sector-by-sector basis, with the Government designating individual markets, industries and sectors to which it applies. Primary legislation will create the overarching framework of the consumer data right, introducing basic obligations that will apply to those within a designated sector. Designations will specify the type of data that is covered and the functionality that is enabled. For example, if the banking and financial services sector were designated, this could apply to specific data such as bank account information and transactions. More detailed obligations will be set out in rules and data standards.
- Security and privacy of consumer data is vitally important. To protect the security of data transfers, consumer privacy and commercial confidentiality, third party data recipients will need to be accredited and a range of information protection safeguards will be introduced.
- Consumer consent and control of their data is central to the consumer data right. Consent must be express (i.e. through a clear opt-in), informed and time-limited, and consumers must be given the ability to review and amend or withdraw consent at any time. Consent for any purpose beyond providing the goods and services the consumer has requested must be optional.
- Consumers will be able to consent to:
- read access – the ability for an accredited person to read consumer data
- action initiation – the ability for an accredited person to carry out an action with the consent of a consumer.
- Action initiation will allow consumers to, for example, ask a third party payment provider to action a bank funds transfer from the consumer’s bank account to a business’s bank account when paying for a goods or services.
- Later in 2021 the Government will make further decisions about the implementation of the consumer data right. This will include decisions on which institutions have a role in implementation and developing rules and standards, and measures for enforcing the consumer data right. The Government will also consider which sectors should be assessed first for the potential application of the consumer data right.
- A Bill implementing the consumer data right will be introduced to Parliament in 2022.
- Senator Elizabeth Warren (D-MA) urged the Commodity Futures Trading Commission (CFTC) “to investigate Google’s “Project Bernanke” and other practices for abuse and manipulation of the online advertising market.” Warren asserted:
- I am particularly concerned about revelations of a secret Google program, Project Bernanke. Court documents have revealed the nature of this scheme whereby Google gathered bid data through its ad exchange, AdX, from other market participants and then used that data to give its own ad-buying systems, DV360 and Google Ads, an advantage over their ad-buying competitors. Because Google was able to learn from rival ad buyers’ previous bidding data, its ad-buying tools gained a competitive advantage that ultimately boosted their win rates. Google’s ad- buying products thus became more attractive than those offered by rivals, killing off other competing ad buyers that could not deliver advertisers the same win rates as Google.
- Approximately 86 percent of online display advertising in the United States is bought and sold in real time on trading venues called ad exchanges. Currently, Google operates the largest ad exchange and dominates the market for tools that publisher-buyers and advertiser-sellers must use to trade. Google’s dominance of these markets for advertisement makes their behavior even more concerning. The House Antitrust Subcommittee already noted the danger of Google’s conflicts of interest in its Digital Markets Report released in 2020. These concerns appear well-founded.
- Court documents about Project Bernanke explain that Google made hundreds of millions of dollars every year through its secret market-abuse strategy. While state and federal enforcers are investigating this activity for potential violations of the antitrust laws, the activity raises additional concerns that I believe may be within the CFTC’s jurisdiction and warrant close scrutiny.
Further Reading
- “Federal Trade Commission expands antitrust powers in Chair Lina Khan’s first open proceeding” By Russell Brandom — The Verge. In an open meeting on Thursday, the Federal Trade Commission passed a pair of pivotal measures expanding its power to regulate anti-competitive business practices, setting the stage for a more aggressive enforcement approach from the embattled agency. Announced last week, Thursday’s proceeding is the first open business meeting of the commission in more than 20 years, as commission proceedings have traditionally been closed to the public. Chair Lina Khan plans to hold public meetings on a monthly basis going forward.
- “How Washington and Big Tech won the global tax fight” By Mark Scott and Emily Birnbaum — Politico. Washington may have fallen out of love with Big Tech. But when it comes to revamping the world’s tax system, the United States backed Silicon Valley against the world. The U.S. government fended off a largely European push to force the likes of Google, Facebook and Amazon to pay more into national coffers worldwide. Instead of targeting digital — and almost exclusively American — companies, Washington succeeded in convincing countries to agree on a tax regime that requires the world’s largest companies, digital or not, to pay more tax in countries wherever they have local operations.
- “The US has reportedly pushed the EU to delay its new digital services tax” — Euronews and AFP. The United States has asked European countries to delay a proposed digital services tax, according to documents reportedly seen by the AFP news agency. Anonymous diplomatic sources told AFP that Washington put its case to selected European capitals, arguing the proposed digital tax could derail work on a planned global minimum tax rate. The new EU tax, to be announced by the European Commission on July 14, “threatens the work undertaken through the OECD/G20 process,” the US document said.
- “Putin signs law forcing foreign social media giants to open Russian offices” — Reuters. President Vladimir Putin has signed a law that obliges foreign social media giants to open offices in Russia, a document published by the government on Thursday showed, the latest move by Moscow to exert greater control over Big Tech. The Russian authorities are keen to strengthen their control of the internet and to reduce their dependence on foreign companies and countries.
- “Calls to stop NSW police trial of national facial recognition system over lack of legal safeguards” By Josh Taylor — The Guardian. New South Wales police officers are testing out the federal government’s controversial facial recognition system to access passport photos as part of criminal investigations, despite legislation governing its use not yet passing parliament. The Australian Human Rights Commission has said that facial recognition technology should not be used for law enforcement in Australia, unless there are effective legal safeguards are in place.
- “Iranian Disinformation Effort Went Small to Stay Under Big Tech’s Radar” By Sheera Frenkel — The New York Times. On June 13, as Benjamin Netanyahu ended his decade-long run as Israel’s prime minister, a Telegram channel dedicated to protesting him hummed with celebration. “And now prison, go to prison,” read a short message below a photoshopped image of Mr. Netanyahu behind bars. The 7,000 followers of the Telegram channel quickly spread the message to other groups and social media apps.
- “Biden silent on municipal broadband as he makes $65B deal with Republicans” By Jod Brodkin — Ars Technica. President Joe Biden announced a $65 billion broadband-deployment deal Thursday with Senate Republicans and Democrats, but he provided no details on whether the plan will prioritize municipal broadband networks as the president originally proposed. Congressional Republicans have tried to ban municipal broadband nationwide, so it’s highly unlikely that they would have agreed to Biden’s stated goal of giving public networks priority over private ISPs in the next big round of government subsidies. Biden in March proposed $100 billion for broadband over eight years and a provision to prioritize “support for broadband networks owned, operated by, or affiliated with local governments, non-profits, and co-operatives—providers with less pressure to turn profits and with a commitment to serving entire communities.”
- “Israeli charged in global hacker-for-hire scheme wants plea deal -court filing” By Raphael Satter, Christopher Bing, and Joel Schectman — Reuters. An Israeli private detective detained in New York since 2019 on charges of involvement in a hacker-for-hire scheme wants a plea deal, according to a letter filed in court by his lawyer. The unusual case has revealed the impacts of a secretive but thriving cyberespionage industry in India.
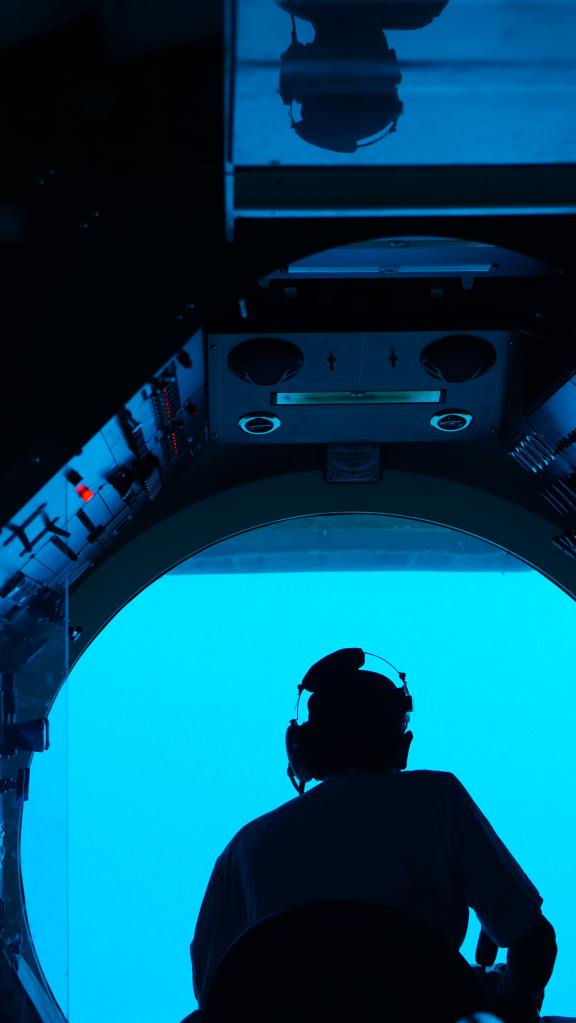
- “How China Steals US Tech to Catch Up in Underwater Warfare” By Ma Xiu and Peter W. Singer — Defense One. In late April, Massachusetts-based businessman Qin Shuren became the latest person to plead guilty in the Justice Department’s crackdown on the illegal export of strategic technologies. Qin’s company, LinkOcean Technologies, falsified documentation to send a Chinese military-affiliated university some $100,000 worth of equipment, including hydrophones, sonobuoys, side-scan sonars, and even an autonomous underwater vehicle (AUV). The case is just one part of a long trail of open-source evidence that illustrates a larger issue: U.S. technology being used to advance Chinese military ends.
- “What does breaking up Big Tech really mean?” By James Surowiecki — MIT Technology Review. For Apple, Amazon, Facebook, and Alphabet, covid-19 was an economic blessing. Even as the pandemic sent the global economy into a deep recession and cratered most companies’ profits, these companies—often referred to as the “Big Four” of technology—not only survived but thrived. Collectively, they now have annual revenue of well over a trillion dollars, and the value of their stocks has soared: together they’re worth $2.5 trillion more than they were 15 months ago. Yet at the same time, they have come under unprecedented attack from politicians and government regulators in the US and Europe. While congressional hearings on charges that Facebook has been censoring conservatives or not doing enough to restrain disinformation and hate speech may have gotten most of the headlines and public attention, the companies are facing far more substantive threats, in the form of new lawsuits, proposed bills, and regulations.
- “Australia-US in talks on space technology treaty” By Joseph Brookes — InnovationAus. The Australian government will negotiate a bilateral treaty with the US for protections of space technology, in a bid to attract more American investment and access to sensitive technology and data into the local market. Controversial fees charged to local companies by the Australian Space Agency for launches will also be delayed a further year in a boost to the local sector.
- “US Secret Service brings back its Cyber Most Wanted list” By Catalin Cimpanu — The Record. The US Secret Service has updated its official website this month to add a new page where the agency is now listing the most sought-after fugitives involved in financially related cybercrime investigations. The new Most Wanted Fugitives page was re-added to the agency’s site after the page had been removed from the site for the past few years.
- “From WhatsApp to William Bligh: The story behind the Archives battle” By Angus Livingston — Sydney Morning Herald. It started with a newsroom discussion about the Prime Minister’s use of Facebook, and it ended with the National Archives getting $67.7 million to save Australia’s crumbling history. The federal government confirmed on Thursday it would pump the money into the National Archives to cover a fast-track digitisation of documents at risk of turning to dust.
- “Team Trump quietly launches new social media platform” By Meridith Mcgraw, Tina Nguyen and Cristiano Lima — Politico. Former President Donald Trump’s team quietly launched a new social media platform on Thursday, billing it as an alternative to Big Tech sites. But the debut immediately ran into confusion about whether it was the former president’s long-promised bid to offer his legions of followers their own social media haven or merely the next attempt to build a MAGA-alternative to the main platforms.
- “Pirates of the cyber seas: How ransomware gangs have become security’s biggest threat” By Chris Zappone — Sydney Morning Herald. Cyber security experts, ex-military officials and some politicians are pushing for ransomware gangs to be treated not as hackers but like “pirates” of the past, in a rethink of how to best counter their growing threat to businesses, industries and society. The shift recognises the way ransomware gangs are used by authoritarian nations to mount sustained attacks on Western businesses and sectors, a new dimension in the ongoing contest between strongmen and democracies.
- “Russian Hackers Mounted Cyber Attack on German Banks, Bild Says” By Patrick Donahue and Jake Rudnitsky — Bloomberg. A hacker group linked to the Russian state known as “Fancy Bear” conducted a cyber attack on critical German infrastructure and the country’s banking system in the past few days, Bild newspaper reported, citing unidentified Western intelligence sources. A spokesman for Germany’s BSI Federal Cyber Security Authority said the agency has no knowledge of such an attack. Bild said the BSI confirmed the hack on Wednesday, and cited unidentified sources as saying it may be revenge for international sanctions leveled on Russia and Belarus.
- “Who’s been looking at your check-in data? We asked the states and territories to ’fess up” By Cam Wilson — Crikey. Police across the country are attempting to access personal data from mandatory COVID-19 check-in apps for reasons other than contact tracing, despite promises that the data would only be used for public health reasons. Police in Queensland, Western Australia and Victoria have all owned up to trying to access logs of data created by Australians using check-in applications as part of their investigations, and enquiries by Crikey suggest that police in other states could also access this data using a warrant.
- “Robots, electric cars and face-scanners: China and the US vie to build the future” By Stephen Bartholomeusz — Sydney Morning Herald. When Chinese Premier Li Keqiang unveiled the “Made in China 2025” 10-year strategic plan in 2015, he laid the foundations for an escalating competition between China and the US to dominate the fourth industrial revolution. The announcement of China’s plans triggered alarm in the US because it confirmed publicly, for the first time, the scope of its ambitions and the detail of its strategies for achieving them.
Coming Events

- The House Appropriations Committee will hold a 13 July markup of its FY 2022 Department of Defense and Homeland Security Appropriations Acts:
- On 13 July, the House Judiciary Committee’s Crime, Terrorism, and Homeland Security Subcommittee will hold a hearing titled “Facial Recognition Technology: Examining Its Use by Law Enforcement.”
- On 13 July, the Federal Communications Commission (FCC) will hold its monthly meeting with this tentative agenda:
- Securing Communications Networks. The Commission will consider a Third Report and Order that would amend the rules for the Secure and Trusted Communications Networks Reimbursement Program consistent with modifications adopted by Congress in the Consolidated Appropriations Act, 2021. The item would also clarify certain aspects of the Reimbursement Program. (WC Docket No. 18-89)
- Enabling State-of-the-Art Radar Sensing Technologies in the 60 GHz Band. The Commission will consider a Notice of Proposed Rulemaking proposing revisions to Section 15.255 of the rules governing short range radar operations in the 64-71 GHz frequency band. (ET Docket No. 21-264)
- Updating Technical Rules for Radio Broadcasters. The Commission will consider a Notice of Proposed Rulemaking to eliminate or amend outmoded or unnecessary broadcast technical rules. (MB Docket No. 21-263)
- Updating International Filing Requirements for the Digital Age. The Commission will consider an Order that would amend rules to require the remaining applications and reports to be filed electronically in the International Bureau Filing System (IBFS) and eliminate duplicative paper filing requirements. (IB Docket No. 21-265)
- Enforcement Bureau Action. The Commission will consider an enforcement action.
- On 14 July, the Senate Energy and Natural Resources Committee will “consider an original bill to invest in the energy and outdoor infrastructure of the United States to deploy new and innovative technologies, update existing infrastructure to be reliable and resilient, and secure energy infrastructure against physical and cyber threats, and for other purposes.”
- The Senate Finance Committee’s Fiscal Responsibility and Economic Growth Subcommittee will hold a hearing titled “Defending and Investing in U.S. Competitiveness” on 14 July.
- The Joint Economic Committee will hold a 14 July hearing titled “A Second Gilded Age: How Concentrated Corporate Power Undermines Shared Prosperity.”
- On 14 July, the Senate Veterans Affairs Committee will hold a hearing titled “VA Electronic Health Records: Modernization and the Path Ahead.”
- On 15 July, the Senate Commerce, Science, and Transportation Committee will convene a hearing titled “Implementing Supply Chain Resiliency.”
- The House Homeland Security Committee will hold a 15 July hearing titled “Securing the Homeland: Reforming DHS to Meet Today’s Threats.”
- On 21 July, the Federal Trade Commission (FTC) will open its monthly open meeting with this agenda:
- Care Labeling Rule: In July 2011, the Commission initiated a regulatory review proceeding of the Care Labeling Rule. As part of the proceeding, the Commission has solicited public comments on multiple proposals to change the rule, including a proposal to repeal the Rule entirely. The Commission will vote on whether to rescind the proposal to repeal the Care Labeling Rule.
- Proposed Policy Statement on Repair Restrictions Imposed by Manufacturers and Sellers: The FTC Act authorizes the Commission to adopt policy statements. The Commission will vote on whether to issue a new policy statement, following the Commission’s “Nixing the Fix” report which was unanimously agreed to and announced on May 6, 2021.
- Policy Statement on Prior Approval and Prior Notice Provisions in Merger Cases: In 1995, the Commission adopted a policy statement regarding “prior approval” and “prior notice” remedies in merger cases. The Commission will vote on whether to rescind this policy statement.
- On 27 July, the Federal Trade Commission (FTC) will hold PrivacyCon 2021.
© Michael Kans, Michael Kans Blog and michaelkans.blog, 2019-2021. Unauthorized use and/or duplication of this material without express and written permission from this site’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to Michael Kans, Michael Kans Blog, and michaelkans.blog with appropriate and specific direction to the original content.
Photo by fotografierende from Pexels
Photo by Aneta Foubíková on Unsplash
Photo by Teo Duldulao on Unsplash
Photo by Alexander Popov on Unsplash