The Comptroller General again finds a number of technology programs and policies to be lacking in the biennial list of risky areas.
The Government Accountability Office (GAO) issued its biennial High-Risk List and a number of technology issues remained at the fore, with some having become more serious since 2019 when the GAO last named its riskiest areas. On the basis of this list, Congress and the Biden Administration will look to act in fulfilling the hundreds of recommendations the GAO has made in years past that remain partially met at best in most cases. And while the GAO named a number of areas that directly bear on United States (U.S.) policy (such as “Strengthening Department of Homeland Security Management Functions” and “Ensuring the Effective Protection of Technologies Critical to U.S. National Security Interests,” I will only focus on cybersecurity and information technology, two areas long the subject of grave concern at the GAO. To reiterate, much of the GAO’s analysis of any of the issues on the High-Risk List is in compiling and integrating previously issued work.
The GAO placed “Ensuring the Cybersecurity of the Nation” among the “High-risk areas that regressed since 2019” and “IT Acquisitions and Operations” in its list of “High-risk areas that need additional attention.” However, “Strengthening Department of Homeland Security Management Functions” and “Ensuring the Effective Protection of Technologies Critical to U.S. National Security Interests” remained at the same risk level as in 2019 when the GAO last issued its list. Additionally, there are other areas the GAO put on its list that pertain to technology law and policy, including “Strategic Human Capital Management”
The GAO took the Trump Administration to task for its failure to provide leadership on cybersecurity issues and also poked the Biden Administration to nominate a National Cyber Director. The GAO stated:
The Ensuring the Cybersecurity of the Nation high-risk area declined from a met rating in 2019 to a partially met rating in 2021 for the criterion of leadership commitment. This regression is due to missing (1) important characteristics of a national strategy in the White House’s September 2018 National Cyber Strategy and the National Security Council’s accompanying June 2019 Implementation Plan and (2) an officially appointed central leader for coordinating the execution of the White House’s approach to managing the nation’s cybersecurity. Such a position was established by statute in January 2021. As of mid-January 2021, the position had not yet been filled.
The GAO provided more detail on how the U.S. is failing to ensure its cybersecurity through a failure of leadership domestically and internationally, the lack of “a comprehensive internet privacy law,” no federal legislation on facial recognition technology, and gaps in federal regulation of privacy:
- In light of the elimination of the White House Cybersecurity Coordinator position in May 2018, it had remained unclear what official within the executive branch is to ultimately be responsible for coordinating the execution of the Implementation Plan and holding federal agencies accountable for the plan’s nearly 200 activities moving forward. In January 2021, Congress enacted a statute that established the Office of the National Cyber Director within the Executive Office of the President.
- The office is to be headed by a Senate-confirmed National Cyber Director and is to, among other things, coordinate cybersecurity policy and operations across the executive branch. Once this position is filled, the White House can (1) ensure that entities are effectively executing their assigned activities intended to support the nation’s cybersecurity strategy, and (2) coordinate the government’s efforts to overcome the nation’s cyber-related threats and challenges.
- It is also important for the United States to have sufficient leadership in building consensus among international organizations regarding internet standards and cultivating norms for acceptable state behavior in cyberspace. In June 2019, the Department of State (State) notified Congress of its intent to establish a new Bureau of Cyberspace Security and Emerging Technologies (CSET) that would focus on cyberspace security and the security aspects of emerging technologies.
- However, we reported in September 2020 that officials from six agencies that work with State on cyber diplomacy issues stated that (1) they were unaware of State’s plan to develop CSET, and (2) being informed of State’s plan for CSET could be helpful for maintaining their communications with State. We recommended in September 2020 that State involve federal agencies that contribute to cyber diplomacy to obtain their views and identify any risks, as it implements its plan to establish CSET.
- We also reported in July 2020 that the United States does not have a comprehensive internet privacy law governing the collection, use, and sale of personal information by private-sector companies. In addition, no federal law expressly regulates the commercial use of facial recognition technology, including the identifying and tracking of individuals.
- Further, in most contexts, federal law does not address how personal data derived from facial recognition technology may be used or shared. As we previously reported, the Federal Trade Commission lacks explicit and comprehensive authority related to privacy issues and the Federal Communications Commission has had a limited role in overseeing internet privacy.
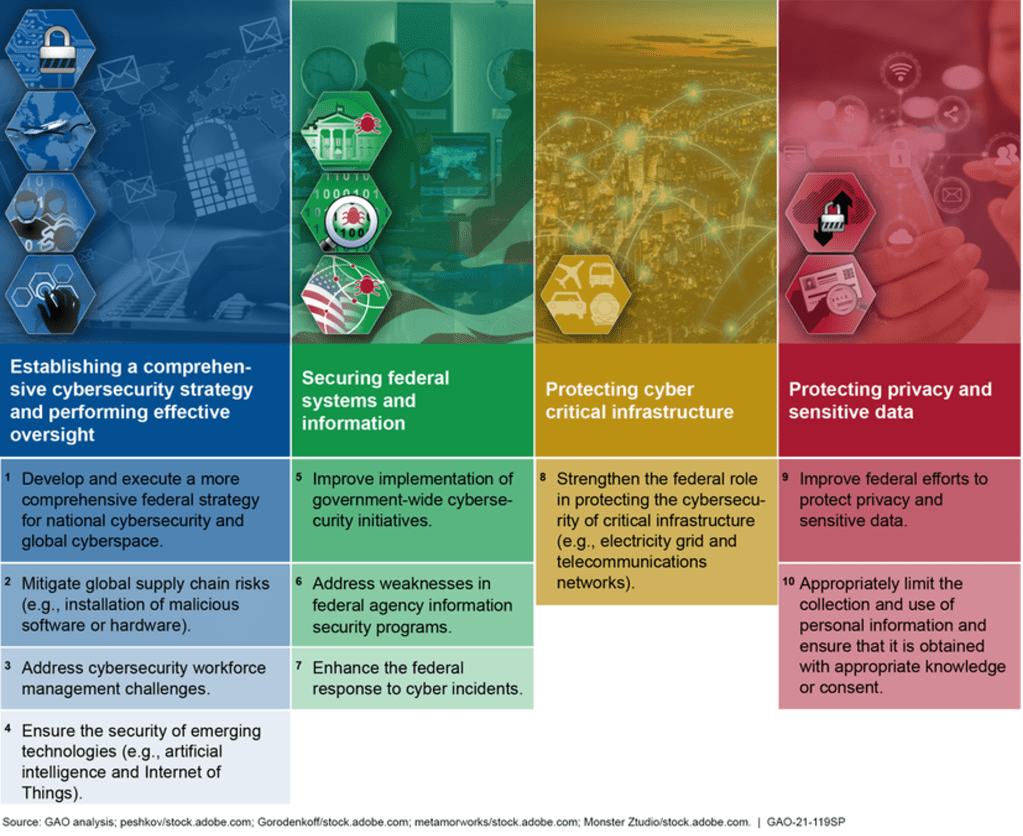
The GAO stated “[b]ased on our prior work, we have identified four major cybersecurity challenges:
- establishing and implementing a comprehensive cybersecurity strategy and performing effective oversight,
- securing federal systems and information,
- protecting cyber critical infrastructure, and
- protecting privacy and sensitive data.
The GAO also made available this infographic titled “Ten Critical Actions Needed to Address Four Major Cybersecurity Challenges:”
The GAO stated “[a]gencies need to urgently address the 10 critical actions to effectively respond to this incident and, thus, better position the nation to prevent, or more quickly detect and mitigate the damage of, future cyberattacks…[i]n particular:
- Develop and execute a more comprehensive federal strategy for national cybersecurity and global cyberspace. As previously mentioned, the position of National Cyber Director needs to be filled to coordinate the execution of a national cyber strategy, including implementing activities necessary to effectively respond to significant cybersecurity incidents.
- Mitigate global supply chain risks. We reported in December 2020 that none of the 23 civilian CFO Act agencies had fully implemented seven selected foundational practices for managing information and communications technology supply chain risks. Those agencies need to address the 145 recommendations that we made to address those weaknesses.
- Enhance the federal response to cyber incidents. In July 2019, we reported that most of 16 selected federal agencies had deficiencies in at least one of the activities associated with incident response processes. We and the inspectors general have made thousands of recommendations aimed at improving information security programs and practices—including those relating to incident response processes over the years; however, many of these recommendations remain unimplemented.
The GAO also reiterated its calls for Congress to act:
- We previously suggested in May 2008 that Congress consider amending laws, such as the Privacy Act of 1974 and the E-Government Act of 2002, because they may not consistently protect personally identifiable information (PII) (i.e., any information that can be used to distinguish an individual’s identity).
- Specifically, we found that while these laws and guidance set minimum requirements for agencies, they may not consistently protect PII in all circumstances of its collection and use throughout the federal government, and may not fully adhere to key privacy principles. However, our suggested revisions to the Privacy Act of 1974 and the E-Government Act of 2002 had not been enacted as of December 2020.
- We also suggested in September 2013 that Congress consider strengthening the consumer privacy framework and review issues such as the adequacy of consumers’ ability to access, correct, and control their personal information, and privacy controls related to new technologies such as web tracking and mobile devices. However, these suggested changes had not been enacted as of December 2020.
A federal privacy statute and a revision of federal laws governing the collection, use, and sharing of PII may not be in the cards anytime soon. On privacy, the two parties have dug in over two issues (whether a federal law will clear away all state laws and whether people would be able to sue entities that violate the new law) and do not seem closer to compromise than they were in the last Congress when this issue was seen as being one of the highest priorities in the technology realm.
The buying, developing, and use of information technology (IT) has long been an issue, for much of the U.S. government’s funding for IT goes to propping up so-called legacy systems. Moreover, there have been questions and disconcerting audits about the track records of many agencies in developing bespoke IT, a process that often runs over budget and schedule and under delivers capabilities. Administrations dating back to President George W. Bush’s have grappled with how to buy and develop IT with progress coming slowly or not at all in some regards. Of course, much of the IT bought and used comes from the private sector, which introduces additional issues into such considerations such as companies selling duplicative licenses to components of an agency instead of one agency-wide license.
Regarding “Improving the Management of IT Acquisitions and Operations,” the GAO asserted:
The federal government currently invests more than $90 billion annually in IT, and the Improving the Management of IT Acquisitions and Operations high-risk area continues to face significant challenges. These challenges include (1) 21 of 24 major federal agencies not modifying their practices to fully address the role of their chief information officers; (2) agencies not documenting modernization plans or not including key elements identified in best practices in their plans; (3) agencies needing to take further action to reduce duplicative IT contracts; (4) GSA and OMB having fewer funds available than anticipated to award to new projects for replacing aging IT systems; and (5) agencies not implementing our remaining 400 open recommendations related to this high-risk area.
The GAO identified how the U.S. government can address IT acquisition and operation:
- The Office of Management and Budget (OMB) and covered federal agencies should continue to fully implement the requirements of the Federal Information Technology Acquisition Reform Act (FITARA) FITARA. Additionally, OMB will need to provide sustained oversight to ensure that agency actions are completed and the desired results are achieved. Beyond implementing FITARA and OMB’s guidance to improve the capacity to address our high-risk area, agencies should implement our remaining 400 open recommendations related to this high-risk area including
- our 2018 recommendations related to improving CIO authorities, as well as 2016 recommendations on improving IT workforce planning practices;
- our 2019 recommendations related to improving cloud computing investment spending and savings data; and
- 11 priority recommendations for agencies to, among other things, report all data center consolidation cost savings to OMB.
- OMB and agencies need to take actions to (1) implement at least 80 percent of our open recommendations related to the management of IT acquisitions and operations and (2) achieve at least 80 percent of the over $6 billion in planned PortfolioStat savings. Lastly, agencies should consider applying effective practices that may better position them to implement FITARA provisions and realize IT management improvements and cost savings.
Notably, the GAO is not directly calling for Congress to further legislate on IT acquisition and operations and instead is pressing for OMB and agencies to fully implement the laws that have already been enacted. However, the continued failure to consistently use the authority Congress has provided suggests that resources and institutional factors may be among the reasons Administrations dating back to President Barack Obama’s has failed to follow through. OMB and agency leadership may lack the funding, staff, and bandwidth to ensure agencies follow through. Moreover, in the zero-sum world of Washington, when one entity gains power, such as enhanced authority for Chief Information Officers, another thinks it must be losing power no matter if the shift may result in a net positive for the entity overall. Hence, this is almost certainly deep resistance inside agencies to allowing some of these changes to move forward.
Technology policy and law are crosscutting across the U.S. government, and the GAO named other areas with these types of problems that present a high level of risk, some of which are:
- Modernizing the U.S. Financial Regulatory System: Treasury should track and prioritize the financial services sector’s cyber risk mitigation efforts and update the sector’s cyber risk mitigation plan with metrics and other information.
- Decennial Census: address cybersecurity weaknesses in a timely manner
- DOD Weapon Systems Acquisition: Implement several recommendations to individual programs related to knowledge-based acquisition practices including (1) fully maturing critical technologies prior to starting development; (2) ensuring program cost estimates are fully compliant with best practices including cost risk assessments; and (3) employing reliability and sustainment planning early in a program’s development to ensure realistic reliability requirements and that sustainment cost targets are met; Implement numerous recommendations to individual military departments and DOD components related to improving acquisition cost, schedule, and performance; Implement guidance for software development that provides specific, required direction on when and how often to involve users early in the development process and to continue involving users through development of related program components; Implement leading practices for managing science and technology programs.
© Michael Kans, Michael Kans Blog and michaelkans.blog, 2019-2021. Unauthorized use and/or duplication of this material without express and written permission from this site’s author and/or owner is strictly prohibited. Excerpts and links may be used, provided that full and clear credit is given to Michael Kans, Michael Kans Blog, and michaelkans.blog with appropriate and specific direction to the original content.
Image by Jackelberry from Pixabay