Subscribe to my newsletter, The Wavelength, if you want the content on my blog delivered to your inbox four times a week before it’s posted here. Other Developments The United Kingdom’s (UK) Investigatory Powers Tribunal (IPT) ruled that a Court of Justice for the European Union (CJEU) ruling is binding on the UK and that … Continue reading Other Developments, Further Reading, and Coming Events (10 August 2021)
Tag: Senate Commerce Committee
Senate’s U.S. Tech Bill Takes Shape
Subscribe to my newsletter, The Wavelength, if you want updates on global technology developments four times a week. The combined legislation Senate committees have crafted to address the United States’ (U.S.) technology industry debuted in the Senate. Twitter One of the few things on which Republicans and Democrats can agree is that action is needed … Continue reading Senate’s U.S. Tech Bill Takes Shape
Other Developments, Further Reading, and Coming Events (18 May 2021)
Subscribe to my newsletter, The Wavelength, if you want updates on global technology developments four times a week. Other Developments The Senate is considering the “Endless Frontier Act” (S.1260) this week and invoked cloture on the motion to proceed by an 86-11 vote, thus setting up a vote to end debate on this stage of … Continue reading Other Developments, Further Reading, and Coming Events (18 May 2021)
Other Developments, Further Reading, and Coming Events (17 May 2021)
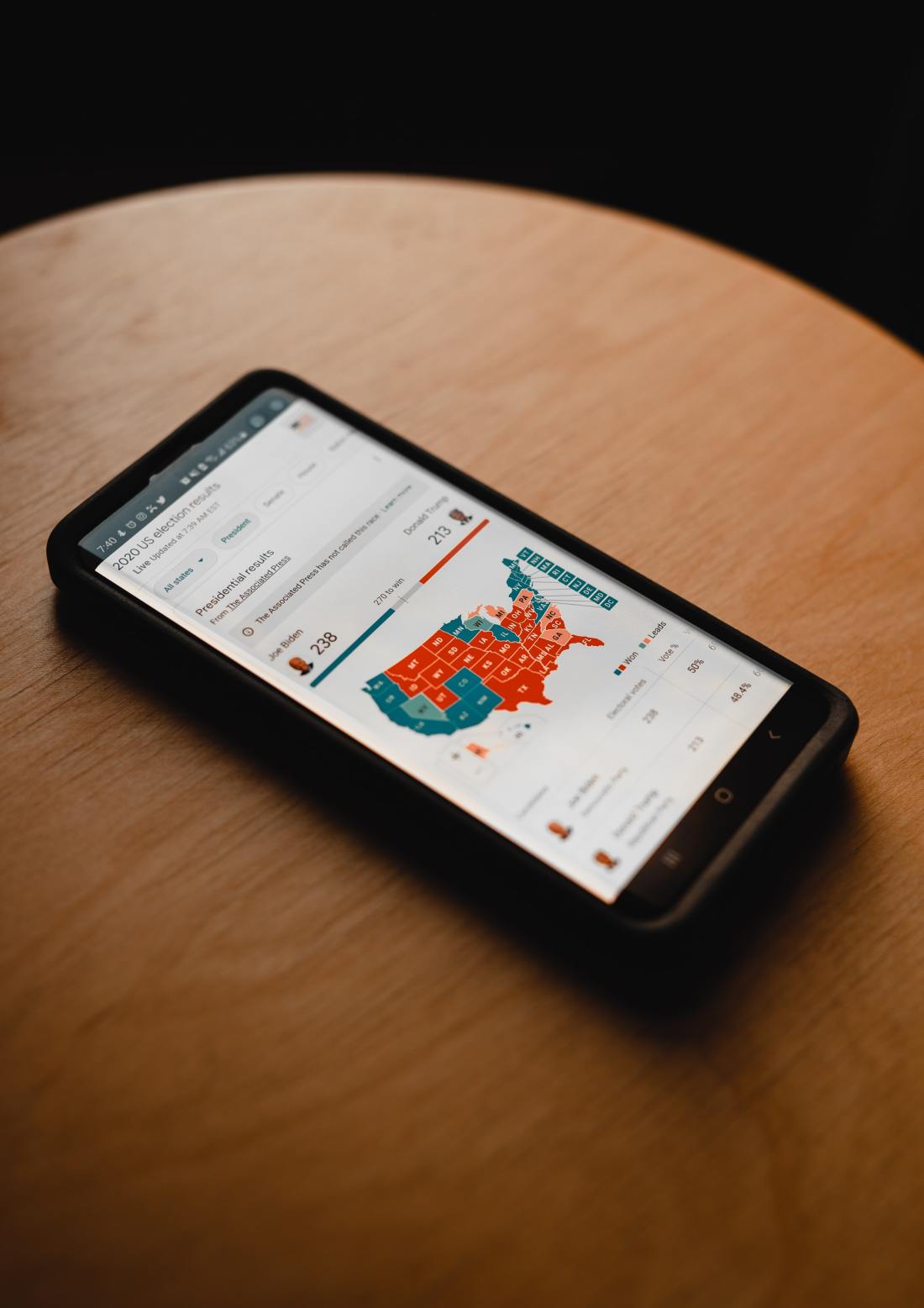
First, subscribe to my newsletter, The Wavelength, if you want all the content on my blog delivered to your inbox four times a week. Other Developments The Senate Rules and Administration Committee met last week to markup its version of the “For The People Act” (S.1), an omnibus voting rights, election security, campaign finance, and … Continue reading Other Developments, Further Reading, and Coming Events (17 May 2021)
Other Developments, Further Reading, and Coming Events (3 May 2021)
First, my first Lawfare article has been posted on data brokering and national security. Second this piece has been cross posted at The Wavelength, my subscription newsletter. Subscribe today if you want to receive these posts in your inbox. Other Developments President Joe Biden gave his first State of the Union address and naturally touched … Continue reading Other Developments, Further Reading, and Coming Events (3 May 2021)
Other Developments, Further Reading, and Coming Events (15, 16, and 17 March 2021)
Other Developments The Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) published a Joint Cybersecurity Advisory (CSA) on the “Compromise of Microsoft Exchange Server.” The agencies stated:The FBI and CISA assess that nation-state actors and cyber criminals are likely among those exploiting these vulnerabilities. The exploitation … Continue reading Other Developments, Further Reading, and Coming Events (15, 16, and 17 March 2021)
Further Reading, Other Developments, and Coming Events ( 1, 2, 3, and 4 March 2021)
Further Reading “Millions of people’s data is at risk’ — Amazon insiders sound alarm over security” — By Vincent Mamancourt — Politico EU. Three whistleblowers are claiming that Amazon has widespread data protection and privacy issues, some of which may violate European Union (EU) or United States (U.S.) law. They claimed the company culture was … Continue reading Further Reading, Other Developments, and Coming Events ( 1, 2, 3, and 4 March 2021)
Further Reading, Other Developments, and Coming Events (3 February 2021)
Further Reading “What We Learned From Apple’s New Privacy Labels” By Brian X. Chen — The New York Times. Another look at the App Store privacy labels Apple has rolled out and how confusing they can be. It can be confusing to compare the privacy and data usage afforded by a developer such that its … Continue reading Further Reading, Other Developments, and Coming Events (3 February 2021)
Further Reading, Other Developments, and Coming Events (2 February 2021)
Further Reading “I checked Apple’s new privacy ‘nutrition labels.’ Many were false.” By Geoffrey Fowler — The Washington Post. It turns out the blue check mark in Apple’s App Store signifying that an app does not collect personal data is based on the honor system. As the Post’s technology columnist learned, Apple tells users this … Continue reading Further Reading, Other Developments, and Coming Events (2 February 2021)
Further Reading, Other Developments, and Coming Events (1 February 2021)
Further Reading “Facebook and Apple Are Beefing Over the Future of the Internet” By Gilad Edelman — WIRED. The battle over coming changes to Apple’s iOS continues to escalate. Apple CEO Tim Cook said the changes that will change the app set up for iPhone users to an opt-in system for tracking people across the … Continue reading Further Reading, Other Developments, and Coming Events (1 February 2021)